China’s Mustang Panda Hackers Exploit TP-Link Routers for Persistent Attacks
By:
May 16, 2023Ravie LakshmananNetwork Security / Threat Intel
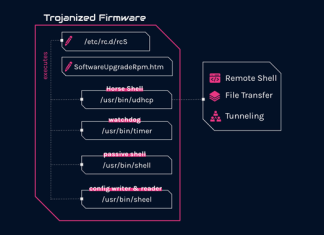
The Chinese nation-state actor known as Mustang Panda has been linked to a new set of sophisticated and targeted attacks aimed...
Researchers Uncover Powerful Backdoor and Custom Implant in Year-Long Cyber Campaign
By:
May 15, 2023Ravie LakshmananCyber Threat / Malware
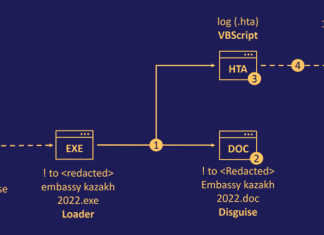
Government, aviation, education, and telecom sectors located in South and Southeast Asia have come under the radar of a new hacking group...
U.S. Government Neutralizes Russia’s Most Sophisticated Snake Cyber Espionage Tool
By:
The U.S. government on Tuesday announced the court-authorized disruption of a global network compromised by an advanced malware strain known as Snake wielded by Russia's Federal Security Service...
Sophisticated DownEx Malware Campaign Targeting Central Asian Governments
By:
May 10, 2023Ravie LakshmananMalware / Cyber Attack
Government organizations in Central Asia are the target of a sophisticated espionage campaign that leverages a previously undocumented strain of malware dubbed...
Meta Uncovers Massive Social Media Cyber Espionage Operations Across South Asia
By:
Three different threat actors leveraged hundreds of elaborate fictitious personas on Facebook and Instagram to target individuals located in South Asia as part of disparate attacks.
"Each of these...
Tonto Team Uses Anti-Malware File to Launch Attacks on South Korean Institutions
By:
Apr 28, 2023Ravie LakshmananMalware / Cyber Threat
South Korean education, construction, diplomatic, and political institutions are at the receiving end of new attacks perpetrated by a China-aligned threat actor...
Paperbug Attack: New Politically-Motivated Surveillance Campaign in Tajikistan
By:
A little-known Russian-speaking cyber-espionage group has been linked to a new politically-motivated surveillance campaign targeting high-ranking government officials, telecom services, and public service infrastructures in Tajikistan.
The intrusion set,...
Kubernetes RBAC Exploited in Large-Scale Campaign for Cryptocurrency Mining
By:
Apr 21, 2023Ravie LakshmananKubernetes / Cryptocurrency
A large-scale attack campaign discovered in the wild has been exploiting Kubernetes (K8s) Role-Based Access Control (RBAC) to create backdoors and run cryptocurrency...
Iranian Government-Backed Hackers Targeting U.S. Energy and Transit Systems
By:
Apr 19, 2023Ravie LakshmananCyber Threat / SCADA
An Iranian government-backed actor known as Mint Sandstorm has been linked to attacks aimed at critical infrastructure in the U.S. between late...
U.S. and U.K. Warn of Russian Hackers Exploiting Cisco Router Flaws for Espionage
By:
Apr 19, 2023Ravie LakshmananNetwork Security / Cyber Espionage
U.K. and U.S. cybersecurity and intelligence agencies have warned of Russian nation-state actors exploiting now-patched flaws in networking equipment from Cisco...