DragonForce Exploits SimpleHelp Flaws to Deploy Ransomware Across Customer Endpoints
The threat actors behind the DragonForce ransomware gained access to an unnamed Managed Service Provider's (MSP) SimpleHelp remote monitoring and management (RMM) tool, and then leveraged it to exfiltrate...
Cybercriminals Target AI Users with Malware-Loaded Installers Posing as Popular Tools
Fake installers for popular artificial intelligence (AI) tools like OpenAI ChatGPT and InVideo AI are being used as lures to propagate various threats, such as the CyberLock and Lucky_Gh0$t...
From Infection to Access: A 24-Hour Timeline of a Modern Stealer Campaign
May 28, 2025The Hacker NewsIdentity Theft / Enterprise Security
Stealer malware no longer just steals passwords. In 2025, it steals live sessions—and attackers are moving faster and more efficiently than...
Iranian Hacker Pleads Guilty in $19 Million Robbinhood Ransomware Attack on Baltimore
May 28, 2025Ravie LakshmananRansomware / Data Breach
An Iranian national has pleaded guilty in the U.S. over his involvement in an international ransomware and extortion scheme involving the Robbinhood ransomware.
Sina...
Hackers Are Calling Your Office: FBI Alerts Law Firms to Luna Moth’s Stealth Phishing...
May 27, 2025Ravie LakshmananData Breach / Social Engineering
The U.S. Federal Bureau of Investigation (FBI) has warned of social engineering attacks mounted by a criminal extortion actor known as Luna...
U.S. Dismantles DanaBot Malware Network, Charges 16 in $50M Global Cybercrime Operation
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of the online infrastructure associated with DanaBot (aka DanaTools) and unsealed charges against 16 individuals for their alleged...
300 Servers and €3.5M Seized as Europol Strikes Ransomware Networks Worldwide
May 23, 2025Ravie LakshmananRansomware / Dark Web
As part of the latest "season" of Operation Endgame, a coalition of law enforcement agencies have taken down about 300 servers worldwide, neutralized...
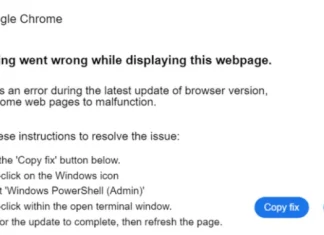
Hackers Use TikTok Videos to Distribute Vidar and StealC Malware via ClickFix Technique
The malware known as Latrodectus has become the latest to embrace the widely-used social engineering technique called ClickFix as a distribution vector.
"The ClickFix technique is particularly risky because it...
FBI and Europol Disrupt Lumma Stealer Malware Network Linked to 10 Million Infections
A sprawling operation undertaken by global law enforcement agencies and a consortium of private sector firms has disrupted the online infrastructure associated with a commodity information stealer known as...
Ransomware Gangs Use Skitnet Malware for Stealthy Data Theft and Remote Access
May 19, 2025Ravie LakshmananRansomware / Malware
Several ransomware actors are using a malware called Skitnet as part of their post-exploitation efforts to steal sensitive data and establish remote control over...