⚡ Weekly Recap: WhatsApp 0-Day, Docker Bug, Salesforce Breach, Fake CAPTCHAs, Spyware App &...
Cybersecurity today is less about single attacks and more about chains of small weaknesses that connect into big risks. One overlooked update, one misused account, or one hidden tool...
Attackers Abuse Velociraptor Forensic Tool to Deploy Visual Studio Code for C2 Tunneling
Cybersecurity researchers have called attention to a cyber attack in which unknown threat actors deployed an open-source endpoint monitoring and digital forensic tool called Velociraptor, illustrating ongoing abuse of...
Webinar: Learn How to Unite Dev, Sec, and Ops Teams With One Shared Playbook
Aug 29, 2025The Hacker NewsCloud Security / Generative AI
Picture this: Your team rolls out some new code, thinking everything's fine. But hidden in there is a tiny flaw that...
Researchers Find VS Code Flaw Allowing Attackers to Republish Deleted Extensions Under Same Names
Aug 28, 2025Ravie LakshmananMalware / Ransomware
Cybersecurity researchers have discovered a loophole in the Visual Studio Code Marketplace that allows threat actors to reuse names of previously removed extensions.
Software supply...
HOOK Android Trojan Adds Ransomware Overlays, Expands to 107 Remote Commands
Cybersecurity researchers have discovered a new variant of an Android banking trojan called HOOK that features ransomware-style overlay screens to display extortion messages.
"A prominent characteristic of the latest variant...
ShadowCaptcha Exploits WordPress Sites to Spread Ransomware, Info Stealers, and Crypto Miners
A new large-scale campaign has been observed exploiting over 100 compromised WordPress sites to direct site visitors to fake CAPTCHA verification pages that employ the ClickFix social engineering tactic...
Anthropic Disrupts AI-Powered Cyberattacks Automating Theft and Extortion Across Critical Sectors
Aug 27, 2025Ravie LakshmananCyber Attack / Artificial Intelligence
Anthropic on Wednesday revealed that it disrupted a sophisticated operation that weaponized its artificial intelligence (AI)-powered chatbot Claude to conduct large-scale theft...
Someone Created the First AI-Powered Ransomware Using OpenAI’s gpt-oss:20b Model
Cybersecurity company ESET has disclosed that it discovered an artificial intelligence (AI)-powered ransomware variant codenamed PromptLock.
Written in Golang, the newly identified strain uses the gpt-oss:20b model from OpenAI locally...
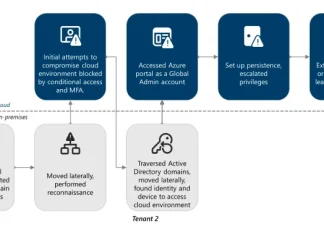
Storm-0501 Exploits Entra ID to Exfiltrate and Delete Azure Data in Hybrid Cloud Attacks
The financially motivated threat actor known as Storm-0501 has been observed refining its tactics to conduct data exfiltration and extortion attacks targeting cloud environments.
"Unlike traditional on-premises ransomware, where the...
Hidden Vulnerabilities of Project Management Tools & How FluentPro Backup Secures Them
Every day, businesses, teams, and project managers trust platforms like Trello, Asana, etc., to collaborate and manage tasks. But what happens when that trust is broken? According to a...