Learn How to Build an Incident Response Playbook Against Scattered Spider in Real-Time
By:
Feb 20, 2024The Hacker NewsWebinar / Incident Response
In the tumultuous landscape of cybersecurity, the year 2023 left an indelible mark with the brazen exploits of the Scattered Spider...
LockBit Ransomware Operation Shut Down; Criminals Arrested; Decryption Keys Released
By:
Feb 20, 2024NewsroomRansomware / Data Protection
The U.K. National Crime Agency (NCA) on Tuesday confirmed that it obtained LockBit's source code as well as intelligence pertaining to its activities...
How Businesses Can Safeguard Their Communication Channels Against Hackers
By:
Efficient communication is a cornerstone of business success. Internally, making sure your team communicates seamlessly helps you avoid friction losses, misunderstandings, delays, and overlaps. Externally, frustration-free customer communication...
U.S. State Government Network Breached via Former Employee’s Account
By:
Feb 16, 2024NewsroomCybersecurity / Data Breach
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has revealed that an unnamed state government organization's network environment was compromised via an administrator...
Microsoft, OpenAI Warn of Nation-State Hackers Weaponizing AI for Cyber Attacks
By:
Feb 14, 2024NewsroomArtificial Intelligence / Cyber Attack
Nation-state actors associated with Russia, North Korea, Iran, and China are experimenting with artificial intelligence (AI) and large language models (LLMs) to...
Microsoft, OpenAI Warn of Nation-State Hackers Weaponizing AI for Cyberattacks
By:
Feb 14, 2024NewsroomArtificial Intelligence / Cyber Attack
Nation-state actors associated with Russia, North Korea, Iran, and China are experimenting with artificial intelligence (AI) and large language models (LLMs) to...
Cybersecurity Tactics FinServ Institutions Can Bank On in 2024
By:
The landscape of cybersecurity in financial services is undergoing a rapid transformation. Cybercriminals are exploiting advanced technologies and methodologies, making traditional security measures obsolete. The challenges are compounded...
Midnight Blizzard and Cloudflare-Atlassian Cybersecurity Incidents: What to Know
By:
Feb 13, 2024The Hacker NewsSaaS Security / Data Breach
The Midnight Blizzard and Cloudflare-Atlassian cybersecurity incidents raised alarms about the vulnerabilities inherent in major SaaS platforms. These incidents illustrate...
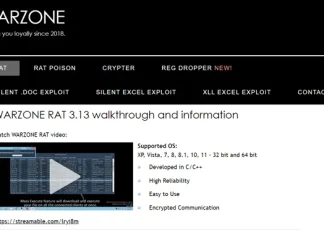
U.S. DoJ Dismantles Warzone RAT Infrastructure, Arrests Key Operators
By:
Feb 11, 2024NewsroomMalware / Cybercrime
The U.S. Justice Department (DoJ) on Friday announced the seizure of online infrastructure that was used to sell a remote access trojan (RAT) called...
After FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
By:
The threat actors behind the KV-botnet made "behavioral changes" to the malicious network as U.S. law enforcement began issuing commands to neutralize the activity.
KV-botnet is the name given...