Twitch Suffers Massive 125GB Data and Source Code Leak Due to Server Misconfiguration
By: Ravie Lakshmanan
Interactive livestreaming platform Twitch acknowledged a "breach" after an anonymous poster on the 4chan messaging board leaked its source code, an unreleased Steam competitor from Amazon Game...
Alert: GhostSec and Stormous Launch Joint Ransomware Attacks in Over 15 Countries
The cybercrime group called GhostSec has been linked to a Golang variant of a ransomware family called GhostLocker.
"TheGhostSec and Stormous ransomware groups are jointly conducting double extortion ransomware attacks...
12,000+ workers’ IDs, banking details, and other personal data leaked by UK staffing agency
We recently discovered an unsecured Microsoft Azure Blob that contains deeply sensitive documents of more than 12,000 construction workers, including scans of passports, national IDs, birth certificates, and tax...
Healthcare Industry Witnessed 45% Spike in Cyber Attacks Since Nov 20
By: Ravie Lakshmanan
Cyberattacks targeting healthcare organizations have spiked by 45% since November 2020 as COVID-19 cases continue to increase globally.
According to a new report published by Check Point Research...
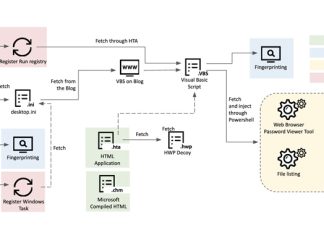
Researchers Uncover Kimusky Infra Targeting South Korean Politicians and Diplomats
By: Ravie Lakshmanan
The North Korean nation-state group Kimusky has been linked to a new set of malicious activities directed against political and diplomatic entities located in its southern counterpart...
Chinese Hackers Targeting South American Diplomatic Entities with ShadowPad
By:
Feb 14, 2023Ravie LakshmananCyber Threat Intelligence
Microsoft on Monday attributed a China-based cyber espionage actor to a set of attacks targeting diplomatic entities in South America.
The tech giant's Security...
Cisco BPA, WSA Bugs Allow Remote Cyberattacks
The high-severity security vulnerabilities allow elevation of privileges, leading to data theft and more.
A set of high-severity privilege-escalation vulnerabilities affecting Business Process Automation (BPA) application and Cisco’s Web Security...
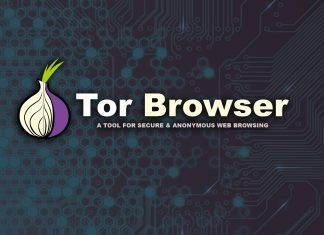
Tracking One Year of Malicious Tor Exit Relay Activities (Part II)
Malicious Tor Exit Relays Using MITM Proxy Attacks on Tor Users
nusenu21 hours ago·19 min read
>25% of the Tor network’s exit capacity has been attacking Tor users
In August 2020 I...
MTTR: The Most Important Security Metric
COMMENTARYReducing risk has long been the guiding principle for security teams. However, even though security teams today are larger with more sophisticated security stacks, risk remains at an all-time...
Indian Government Publishes Draft of Digital Personal Data Protection Bill 2022
By: Ravie Lakshmanan
The Indian government on Friday released a draft version of the much-awaited data protection regulation, making it the fourth such effort since it was first proposed in...