By: Eric C
Being ever-evolving as an attack tool, even the simplest form of ransomware can cost significant time and money, but more severe attacks can deal a crippling blow and even destroy a company completely, sparing no one — not even large, prominent organizations. Unprepared users and businesses can quickly lose valuable data and money from these attacks. This is especially dangerous in these days of economic uncertainty, as both individuals and businesses try to manage and mitigate their risks while planning ahead.
There is no easy win in the war on cyber extortion, and the only way to deal with this threat is to first have proper intelligence — understanding how ransomware works, who it targets, how, and where.
The following facts, statistics, and trends will help you realize how imminent the ransom threat is to your business and personal life.
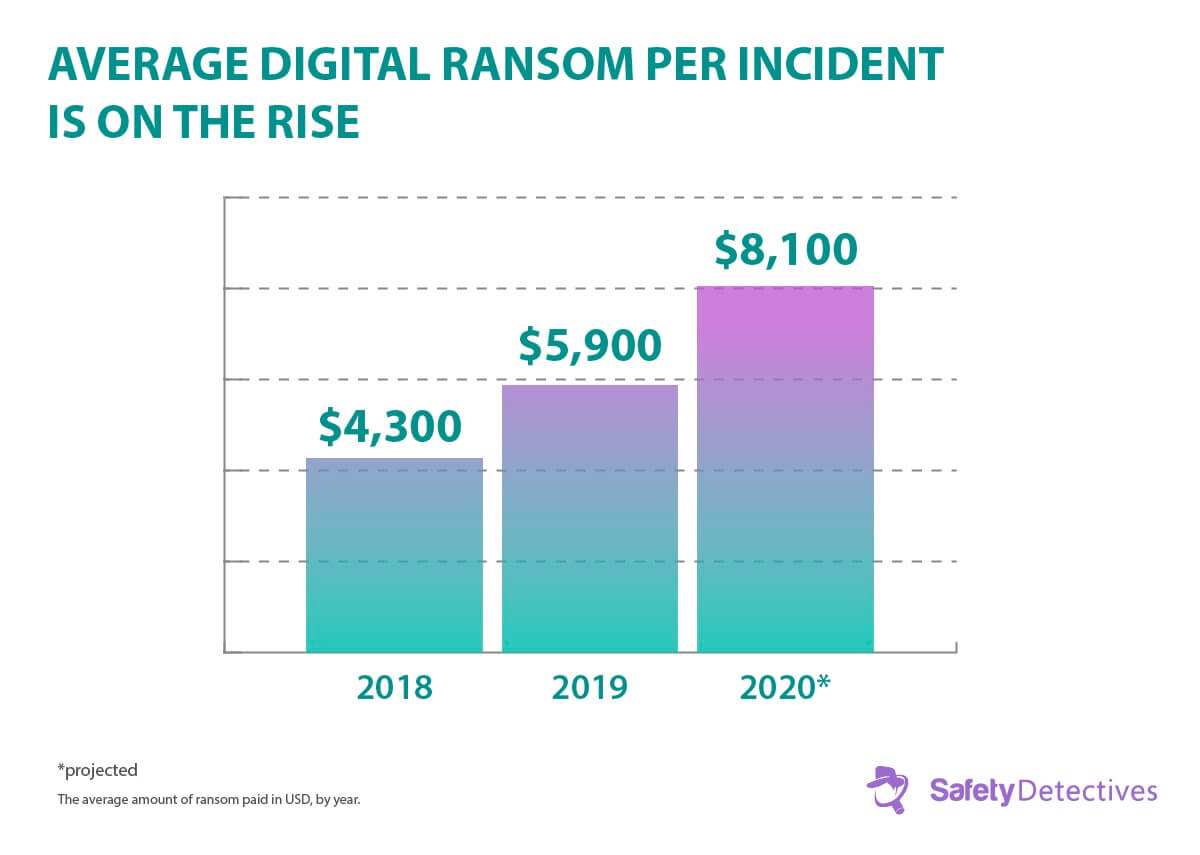
The average ransom payment has nearly doubled over the years, and this trend shows no signs of slowing down. While a few thousand dollars may seem insignificant for larger businesses, it can be crippling for smaller businesses that cannot afford to lose their data. Remember that hackers tend to duplicate successful attacks and hit victims over and over again.
Some hackers even corrupt and delete a company’s files while they await the ransom payment, just to show that they’re serious. Regardless of the cyber criminal’s ultimate actions, the actual cost of ransomware goes beyond just the payout.
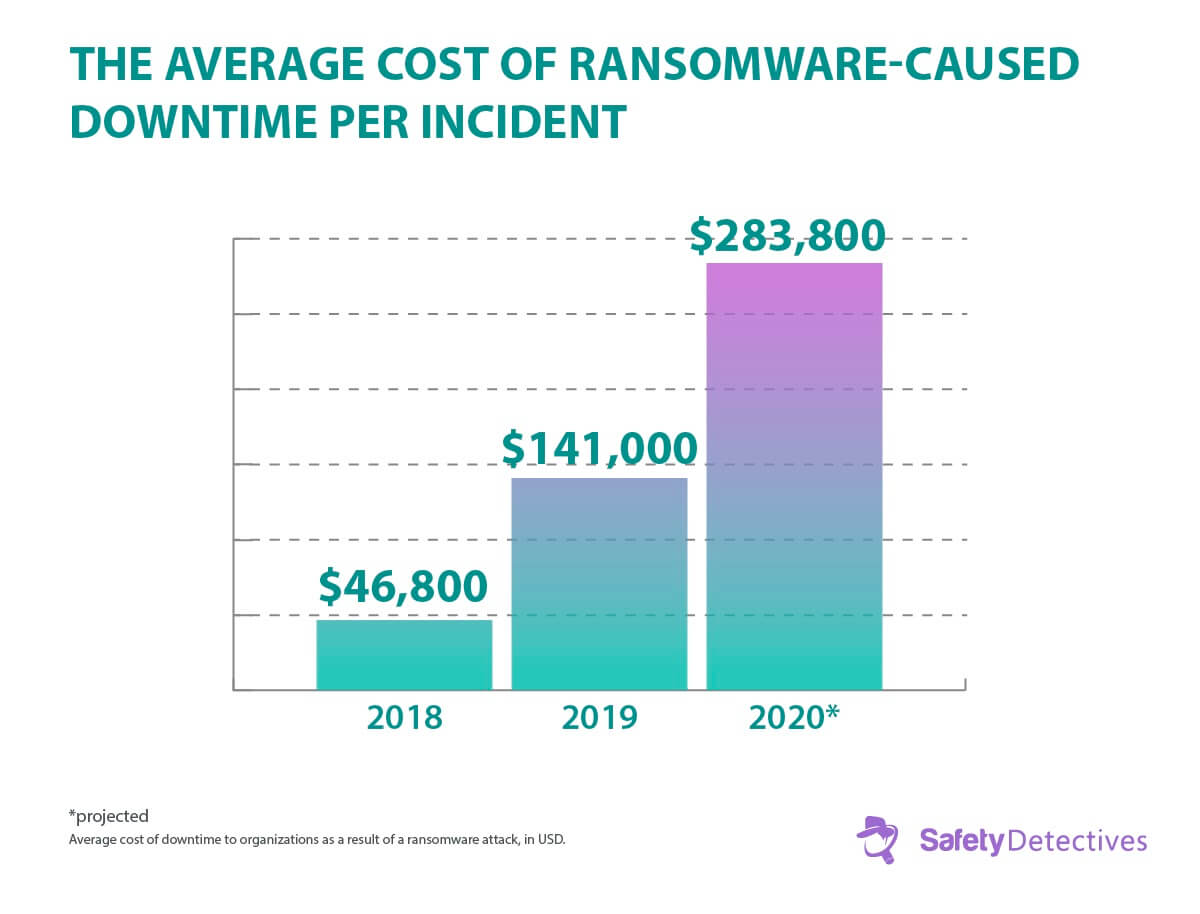
Digital extortion by hackers ultimately inflicts more monetary damage than what the hackers may take in from an attack. Most companies say they’ve experienced data loss and major downtime as the result of a ransomware attack. Both of these outcomes are extremely costly for a business, especially larger ones with hundreds of employees.
Significant downtime can result in millions of dollars in lost revenue. Even worse, it also causes a decrease in consumer trust, especially in cultures that value their relationships with the organizations with whom they have a connection, which will damage future business as well.

Even countries with access to the most advanced security technologies and higher awareness of cyber threats can succumb to such digital extortion. As you see, in the United States, over half of businesses have reported being attacked by ransomware in the last year.
Saudi Arabia, Turkey, and China are the top three countries experiencing ransomware driven incidents, putting their trustworthiness, reputation, and, therefore, businesses at risk.
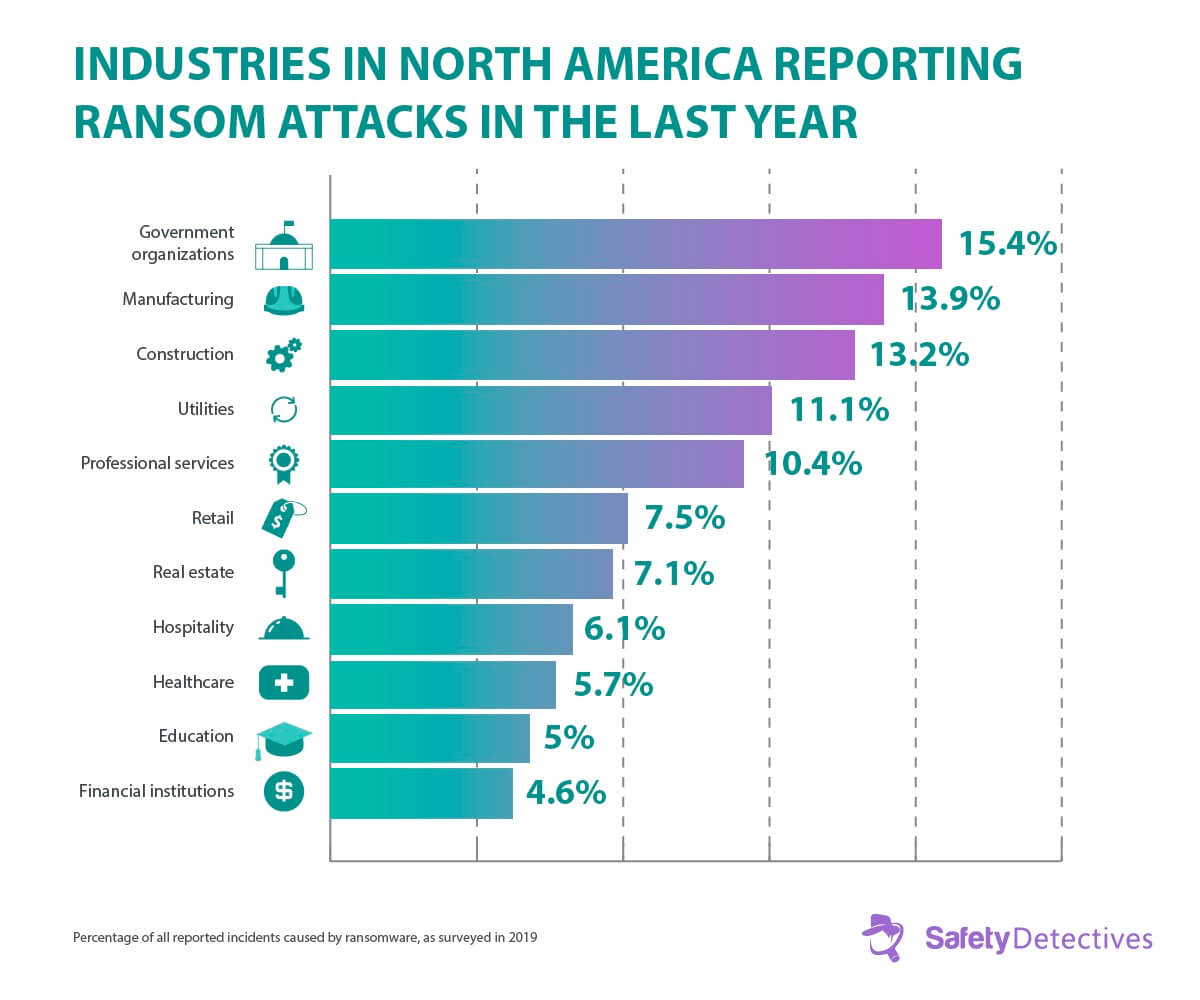
Of all organizations experiencing ransomware attacks in North America, government bodies are the most commonly attacked — at 15.4%, while the manufacturing and construction services industries follow closely behind at 13.9% and 13.2%, respectively.
Governments are being targeted, because a successful attack will impact many lives, increasing the chance of the ransom being paid. For example, the City of Atlanta was shut down for 5 days after an attack blacked out nearly 8,000 computers. Even after the ransom was paid, it took weeks for work to resume as usual. Government organizations are further prone to incidents due to their consistent lack of cybersecurity preparedness when compared to the private-sector.
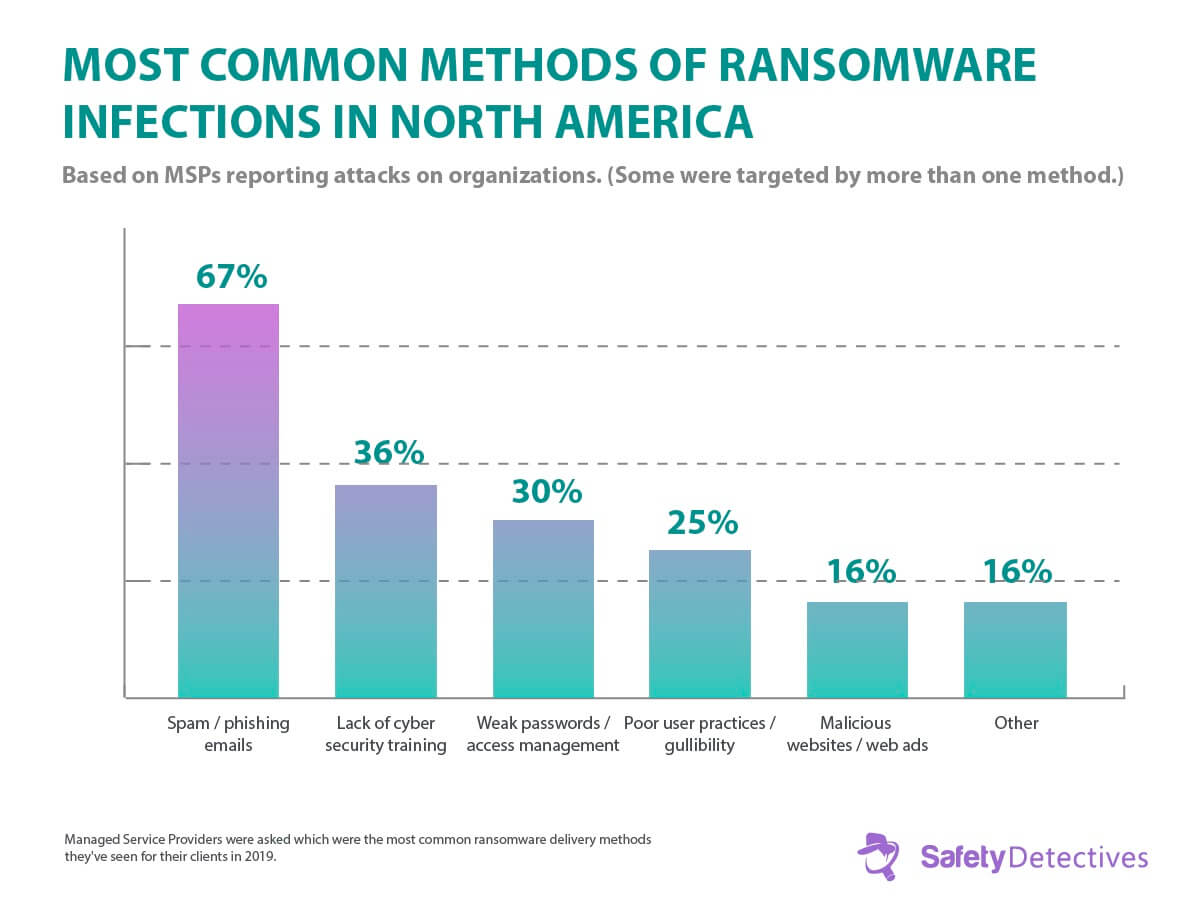
Even though it is well known that emails are a main infection method for all types of cyber attacks, people are still falling victim to malicious social engineering, and in doing so, infecting whole systems with dangerous ransomware.
Lack of training in basic cybersecurity practices, such as reusing weak passwords, lack of proper access management, and poor user awareness as a whole are the causes of ransomware infection.
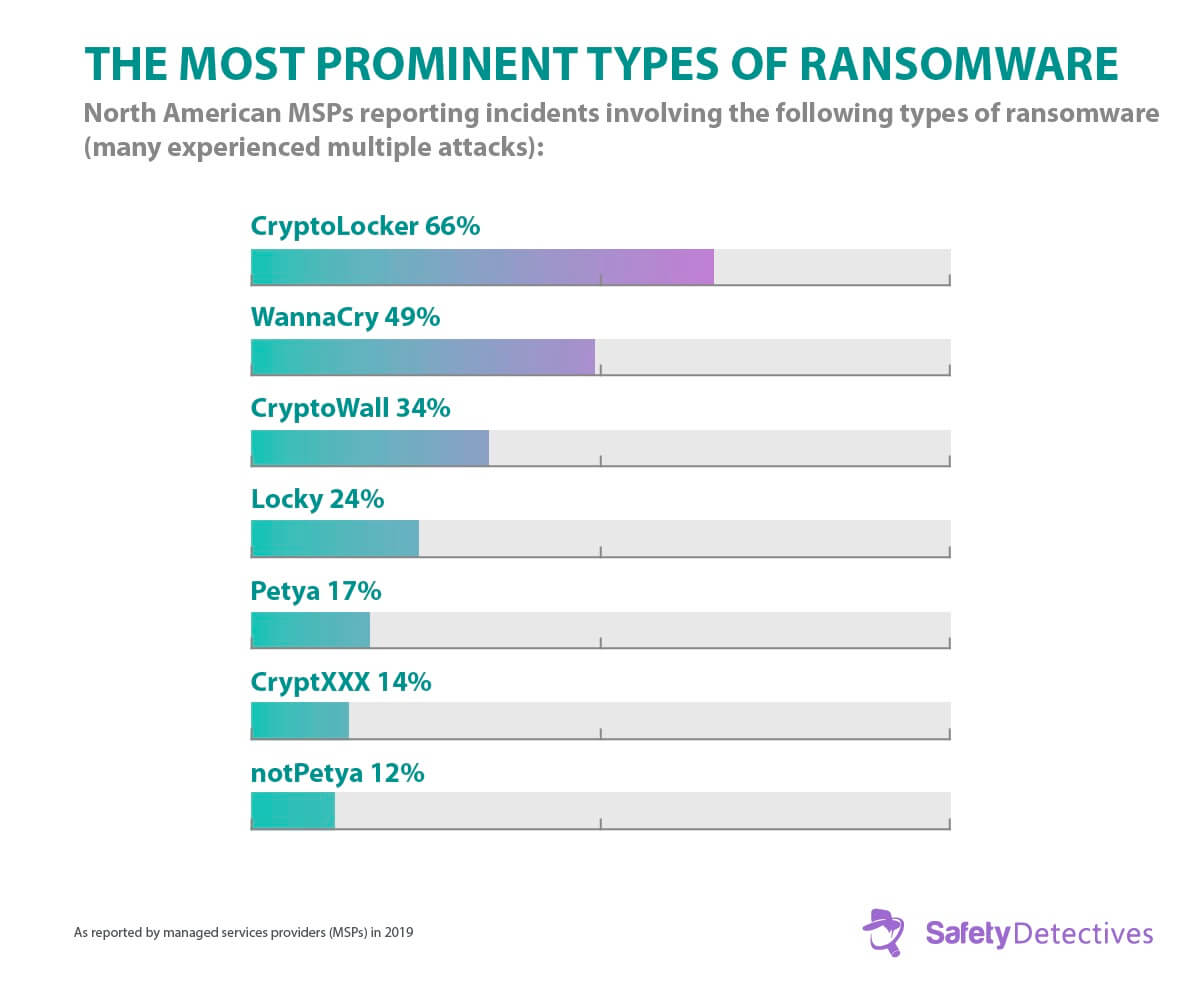
Ransomware is relatively new and it’s constantly evolving, with more sophisticated strains on the rise. Over the last year, the number of new variants increased by 46%. However, we are still seeing the prominence of more well-publicized ransomware.
WannaCry, for example, made international headlines in 2017, taking down systems associated with world government organizations, public transportation, national telecommunication companies, global logistic companies, and multiple universities. Three years later, this purportedly North Korean ransomware still shows its face in nearly half of reported incidents in the U.S. alone.
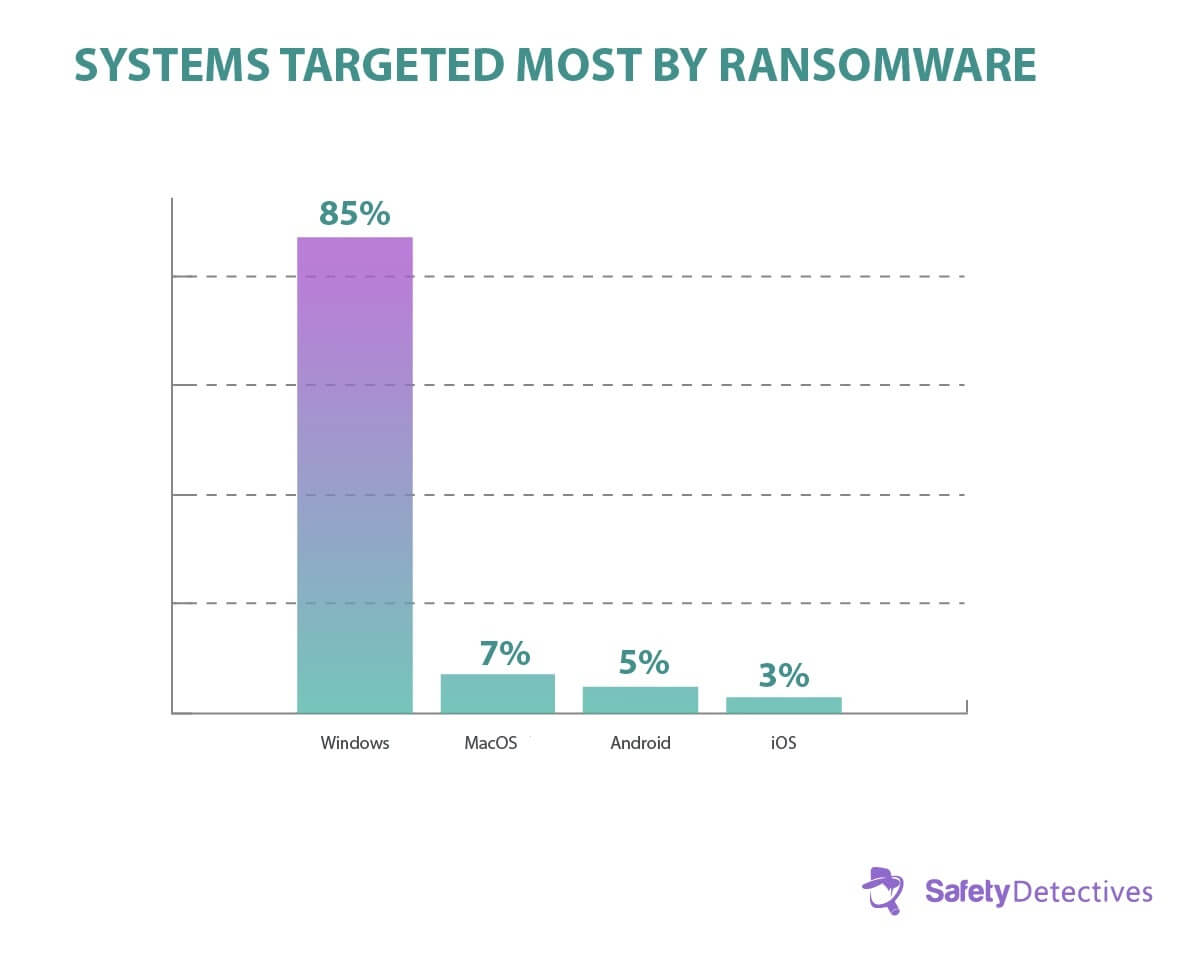
Eighty-five percent of managed service providers (MSPs) say the Windows OS is targeted most frequently by ransomware attacks. The reason? Windows-based computers are typically more affordable, therefore more people use them. There are also enough people who use them that don’t install necessary updates for their operating systems, leaving them without patches that protect against these viruses. This makes them an easy target for online bad actors.
Nonetheless, this doesn’t mean that macOS, Android, and iOS are immune. Remember, it takes only one device a whole company and its systems.
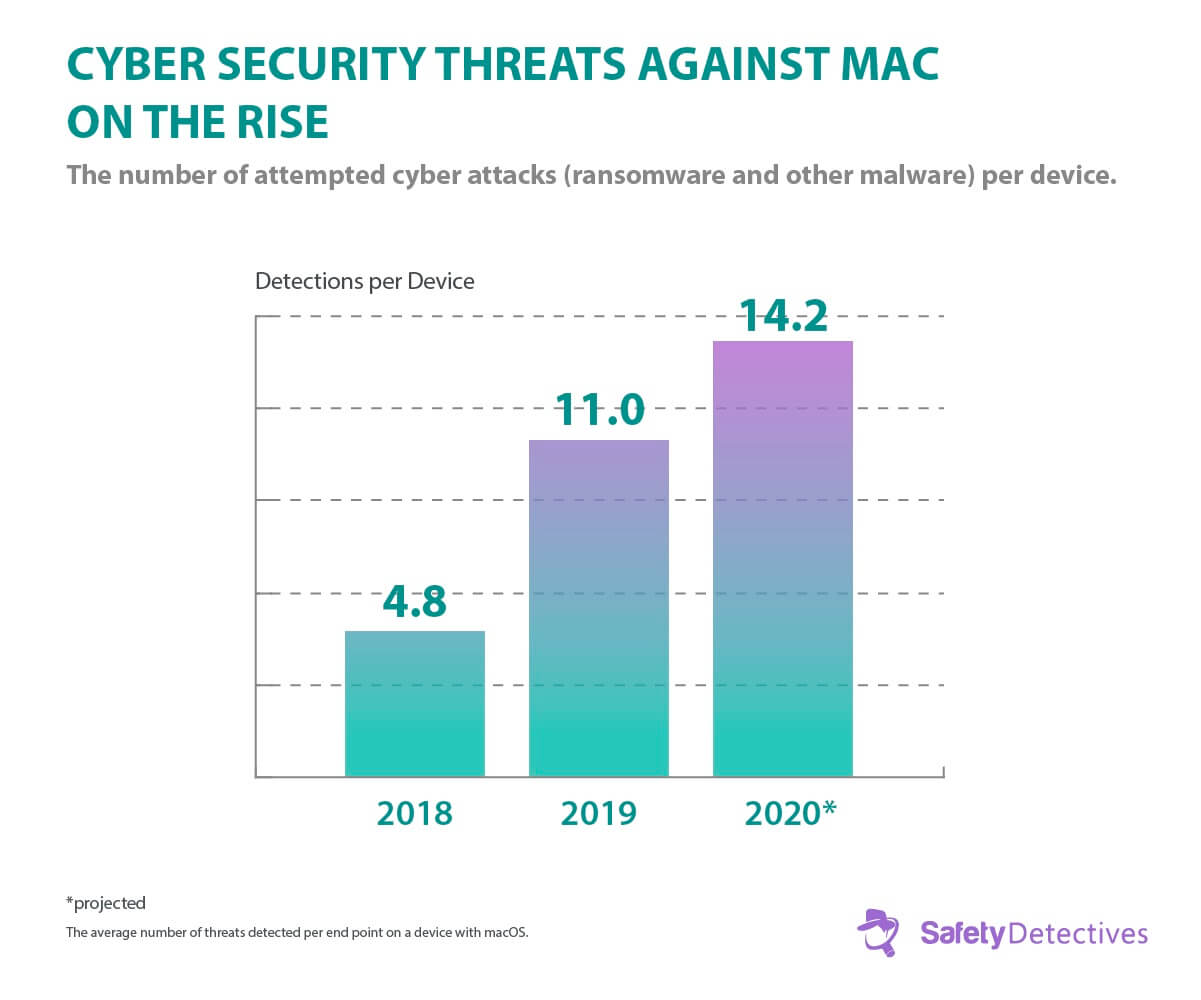
Mac users are no longer safe: Threat detection on Mac devices more than doubled from 2018 to 2019, and that rise is expected to continue. The increasing prominence of these devices even at a higher price point than the competitors makes them a potentially more profitable target for the right cyber criminal.
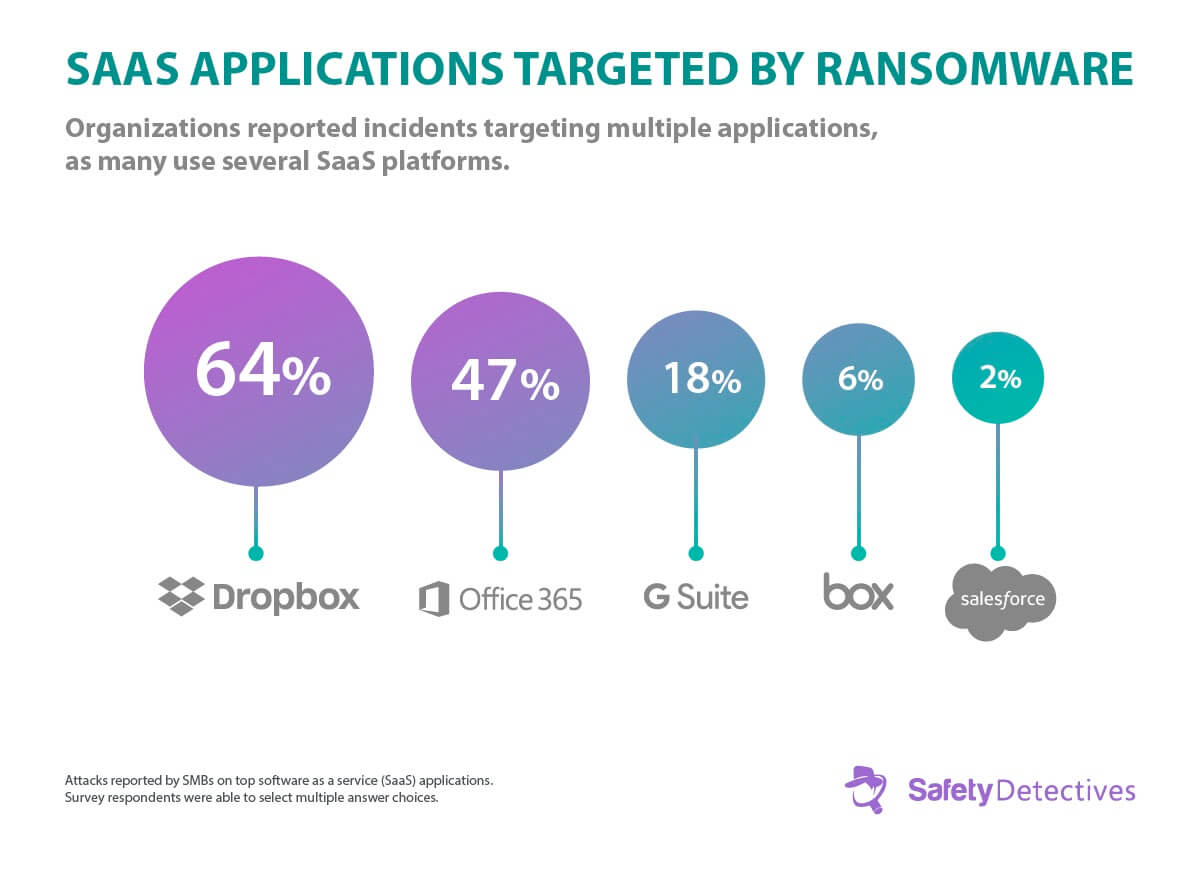
Popular software as a service (SaaS) applications are being targeted by ransomware, too. A study involving several multiple service providers found that Dropbox, Office 365, G Suite, Box, and Salesforce have experienced ransomware attacks in some form.
How does this happen? It typically is due to a lack of proper cybersecurity procedure, or one that was poorly implemented. These apps are virtual treasure troves of organizational data, and an outside party accessing them poses a serious threat to businesses, non-profits, and governments alike.
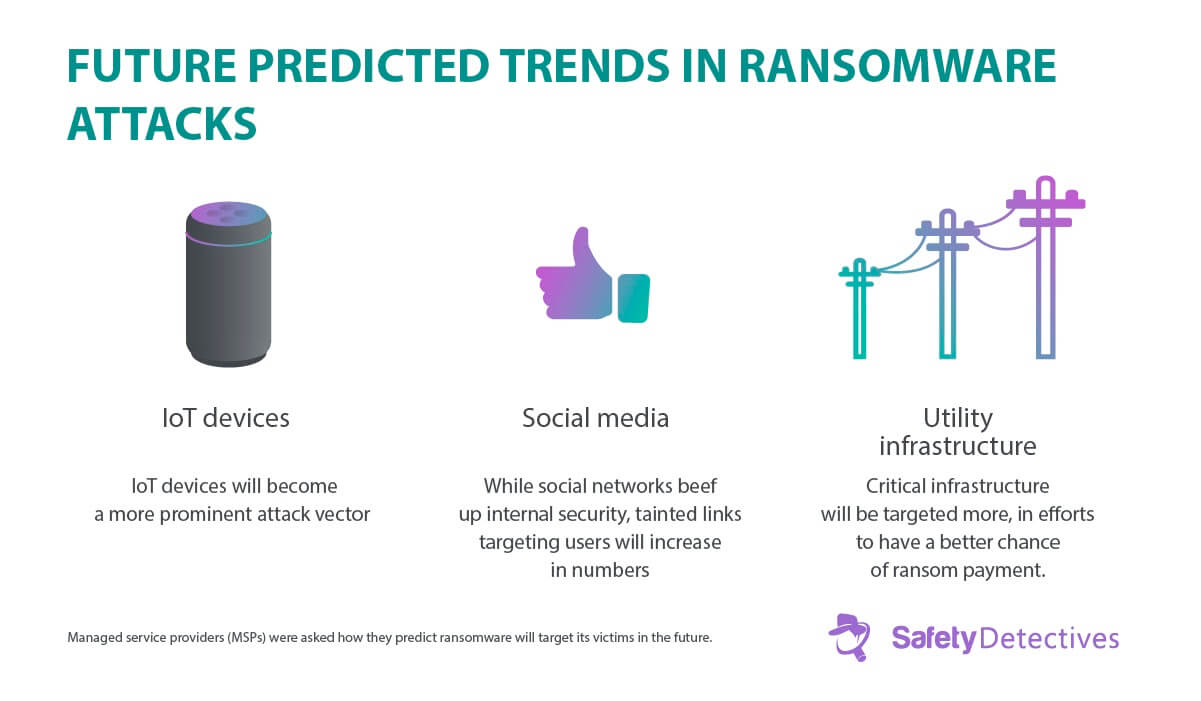
Ransomware isn’t going away any time soon.
Quite simply, it works, so individual users and businesses will continue to be targeted. URLs embedded in emails remains the number one way for computers to become infected.
Data loss is a serious concern that affects both individuals and companies. The best defense against ransomware is for users to learn what it is, how it infects a computer, and what to do once it happens.
Of course, the most effective tool against any type of malicious software is an up-to-date antivirus and or end point protection.












