By:
Oct 20, 2023NewsroomMalvertising / Cyber Threat
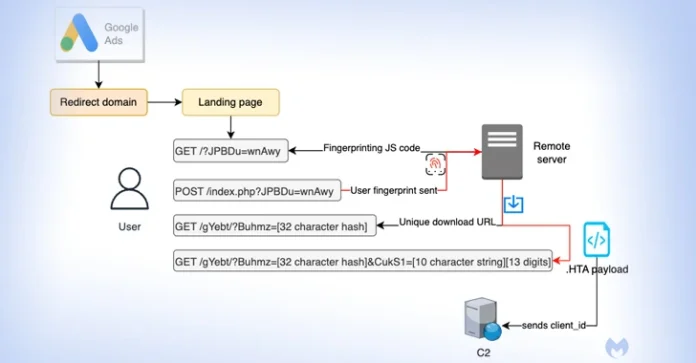
Details have emerged about a malvertising campaign that leverages Google Ads to direct users searching for popular software to fictitious landing pages and distribute next-stage payloads.
Malwarebytes, which discovered the activity, said it’s “unique in its way to fingerprint users and distribute time sensitive payloads.”
The attack singles out users searching for Notepad++ and PDF converters to serve bogus ads on the Google search results page that, when clicked, filters out bots and other unintended IP addresses by showing a decoy site.
Should the visitor be deemed of interest to the threat actor, the victim is redirected to a replica website advertising the software, while silently fingerprinting the system to determine if the request is originating from a virtual machine.
Users who fail the check are taken to the legitimate Notepad++ website, while a potential target is assigned a unique ID for “tracking purposes but also to make each download unique and time sensitive.”
The final-stage malware is an HTA payload that establishes a connection to a remote domain (“mybigeye[.]icu”) on a custom port and serves follow-on malware.
“Threat actors are successfully applying evasion techniques that bypass ad verification checks and allow them to target certain types of victims,” Jérôme Segura, director of threat intelligence, said.
“With a reliable malware delivery chain in hand, malicious actors can focus on improving their decoy pages and craft custom malware payloads.”
The disclosure overlaps with a similar campaign that targets users searching for the KeePass password manager with malicious ads that direct victims to a domain using Punycode (keepass[.]info vs. ķeepass[.]info
), a special encoding used to convert Unicode characters to ASCII.
“People who click on the ad will be redirected via a cloaking service that is meant to filter sandboxes, bots and anyone not deemed to be a genuine victim,” Segura noted. “The threat actors have set up a temporary domain at keepasstacking[.]site that performs the conditional redirect to the final destination.”
Users who land on the decoy site are tricked into downloading a malicious installer that ultimately leads to the execution of FakeBat (aka EugenLoader), a loader engineered to download other malicious code.
The abuse of Punycode is not entirely novel, but combining it with rogue Google Ads is a sign that malvertising via search engines is getting more sophisticated. By employing Punycode to register similar domain names as a legitimate site, the goal is to pull off a homograph attack and lure victims into installing malware.
“While Punycode with internationalized domain names has been used for years by threat actors to phish victims, it shows how effective it remains in the context of brand impersonation via malvertising,” Segura said.
Speaking of visual trickery, multiple threat actors – TA569 (aka SocGholish), RogueRaticate (FakeSG), ZPHP (SmartApeSG), ClearFake, and EtherHiding – have been observed taking advantage of themes related to fake browser updates to propagate Cobalt Strike, loaders, stealers, and remote access trojans, a sign that these attacks are a constant, evolving threat.
“Fake browser updates abuse end user trust with compromised websites and a lure customized to the user’s browser to legitimize the update and fool users into clicking,” Proofpoint researcher Dusty Miller said in an analysis published this week.
“The threat is only in the browser and can be initiated by a click from a legitimate and expected email, social media site, search engine query, or even just navigating to the compromised site.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.