By:
Aug 03, 2023THNCyber Attack / Data Safety
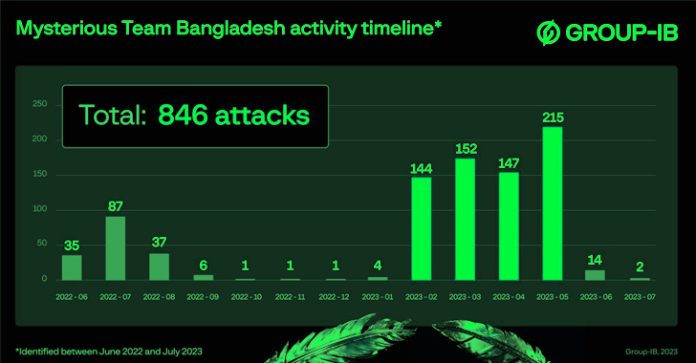
A hacktivist group known as Mysterious Team Bangladesh has been linked to over 750 distributed denial-of-service (DDoS) attacks and 78 website defacements since June 2022.
“The group most frequently attacks logistics, government, and financial sector organizations in India and Israel,” Singapore-headquartered cybersecurity firm Group-IB said in a report shared with The Hacker News. “The group is primarily driven by religious and political motives.”
Some of the other targeted countries include Australia, Senegal, the Netherlands, Sweden, and Ethiopia.
In addition, the threat actor is said to have gained access to web servers and administrative panels, likely by exploiting known security flaws or poorly-secured passwords.
Mysterious Team Bangladesh, as the name indicates, is suspected to be of Bangladeshi origin. “We are working to protect Our Bangladesh Cyberspace,” the group’s Intro on Facebook reads.
The group has an active social media presence across Telegram and Twitter. Its LinkedIn profile lists “Operation Israel” as an ongoing project since June 2022, claiming it supports Palestine, that the “Israeli Government killing & torturing Palestine people’s,” and that “we will attacking their cyberspace until they stop killing Palestine People’s.”
Details about the threat actor first emerged in late 2022 when CloudSEK revealed its plans to attack entities in India. A December 2022 attack on India’s Central Board of Higher Education (CBHE) systems led to the exposure of personally identifiable information such as government identification numbers. It has since been attributed to DDoS attacks on several UAE government websites.
The very first attack campaign against India took place on June 22, 2022, with the group showcasing an affinity for government resources and the websites of banks and financial organizations.
“The renaissance of hacktivism across the globe may have its roots in the ongoing geopolitical conflict, during which hacktivists have carried out multiple campaigns,” the company said.
“As can be seen, modern hacktivist groups are less motivated by any ideology but strive to develop their own brand and recognition in order to subsequently monetize their information resources through the sale of advertising.”
The findings come as a pro-Russian hacktivist collective dubbed NoName057(16) has been linked to a fresh wave of disruptive DDoS attacks on Spanish and Italian websites in recent weeks.
“What is new about NoName057(16)’s DDoSia attacks is that the group admins perform reconnaissance before staging their attack vectors,” Radware said in a Wednesday analysis. “They investigate the target website and identify the most resource-intensive parts of the site.
“Pages with a search function or a form to fill in are typical candidates. NoName057(16) records all the variables used by GET and POST requests for those pages, including any cookies and potential captcha keys, and then crafts specific web requests with placeholders for random data to be leveraged as attack vectors.”
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.