PandaStealer is delivered in rigged Excel files masquerading as business quotes, bent on stealing victims’ cryptocurrency and other info.
Yet another new information stealer – Panda Stealer – is being spread through a worldwide spam campaign.
On Tuesday, Trend Micro researchers said that they first spotted the new stealer in April. The most recent wave of the spam campaign has had the biggest impact in Australia, Germany, Japan and the U.S.
The spam emails are masquerading as business-quote requests to lure victims into clicking on booby-trapped Excel files. The researchers found 264 files similar to Panda Stealer on VirusTotal, with some of them being shared by threat actors on Discord.

Join Threatpost for “Fortifying Your Business Against Ransomware, DDoS & Cryptojacking Attacks” a LIVE roundtable event on Wednesday, May 12 at 2:00 PM EDT for this FREE webinar sponsored by Zoho ManageEngine.
That’s not surprising, given recent trends: Cisco’s Talos cybersecurity team recently found that threat actors have infiltrated workflow and collaboration tools like Slack and Discord to slip past security and deliver info-stealers, remote-access trojans (RATs) and other malware.
… Or Maybe Collaborating on More of the Same
Then again, threat actors could also be using Discord to share the Panda Stealer build with each other, Trend Micro suggested.
Once Panda gets cozy, it tries to hoover up details such as private keys and past transactions from cryptocurrency wallets, including Bytecoin (BCN), Dash (DASH), Ethereum (ETH) and Litecoin (LTC). Beyond stealing wallets, it can also filch credentials from applications, including NordVPN, Telegram, Discord and Steam. Panda can also take screenshots of the infected computer and swipe data from browsers, including cookies and passwords.
The researchers discovered two ways that the spam infects victims: In one infection chain, an .XLSM attachment contains macros that download a loader, which executes the main stealer. In another infection chain, an .XLS attachment containing an Excel formula triggers a PowerShell command to access paste.ee, a Pastebin alternative that in turn accesses a second encrypted PowerShell command. The image below shows an Excel formula accessing a paste.ee URL via PowerShell command:
All in the Stealer Family
Panda Stealer is a tweak of the malware Collector Stealer, also known as DC Stealer, which has been found selling on an underground forum and via Telegram for as little as $12. It’s advertised as a “top-end information stealer” and has a Russian interface.
A threat actor called NCP, also known as su1c1de, has actually cracked Collector Stealer. The cracked stealer and Panda Stealer behave similarly, but they don’t share the same command-and-control (C2) URLs, build tags or execution folders. But both exfiltrate information like cookies, login data and web data from a compromised computer, storing them in an SQLite3 database.
The cracked Collector Stealer is freely available online, meaning that it’s easy to get it, tweak it and let it rip.
“Cybercriminal groups and script kiddies alike can use it to create their own customized version of the stealer and C2 panel,” Trend Micro researchers said. “Threat actors may also augment their malware campaigns with specific features from Collector Stealer.”
Fileless Distribution Covers the Scent
Besides cribbing from Collector Stealer, Panda Stealer has borrowed from another piece of malware: Namely, it uses the same fileless distribution method as the “Fair” variant of Phobos ransomware to slip past detection. In other words, it runs in memory after initial infection, instead of storing files on the hard drive.
Dimiter Andonov, senior principal reverse engineer for Mandiant, told Threatpost in an email on Tuesday that the use of the fileless technique is a hallmark of advanced malware techniques.
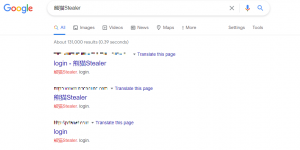
Panda drops files in targeted systems’ Temp folders, storing stolen information under randomized file names. Then, it exfiltrates the stolen data and sends it to a C2 server. When analyzing that C2 server, researchers were led to a login page for “熊猫Stealer,” which translates to “Panda Stealer,” though they found more domains that share that same login page. The image below shows other login pages called “熊猫Stealer:”
Researchers found 14 victims listed on the logs for one of those servers. They also found an IP address that they think the threat actor was using: It was hosted on a virtual private server (VPS) rented from Shock Hosting that had been compromised for testing purposes. After researchers reported their find to Shock Hosting, it suspended the server.
Join Threatpost for “Fortifying Your Business Against Ransomware, DDoS & Cryptojacking Attacks” – a LIVE roundtable event on Wed, May 12 at 2:00 PM EDT. Sponsored by Zoho ManageEngine, Threatpost host Becky Bracken moderates an expert panel discussing best defense strategies for these 2021 threats. Questions and LIVE audience participation encouraged. Join the lively discussion and Register HERE for free.