By:
Bradley Barth
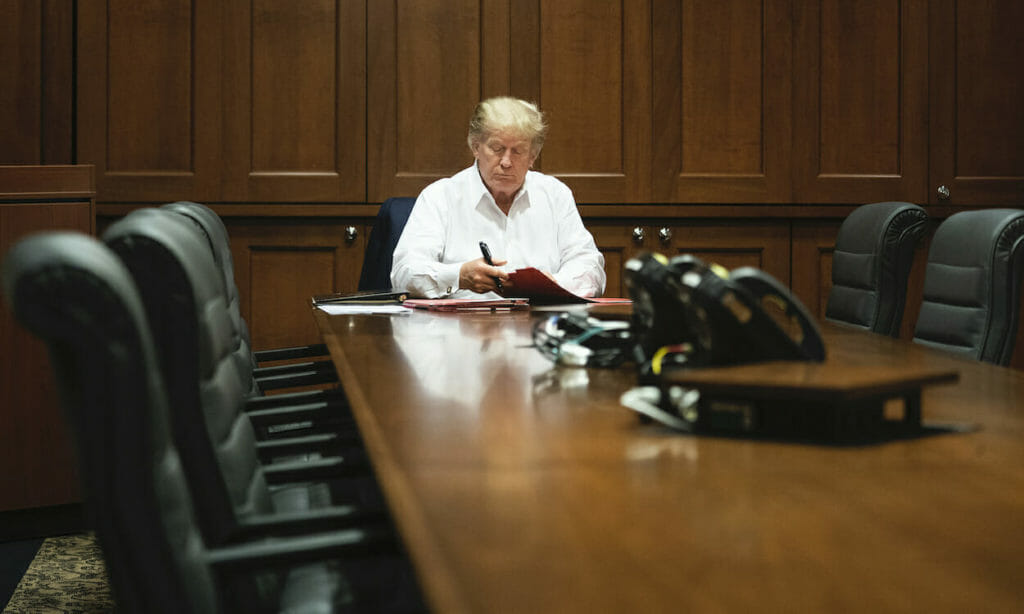
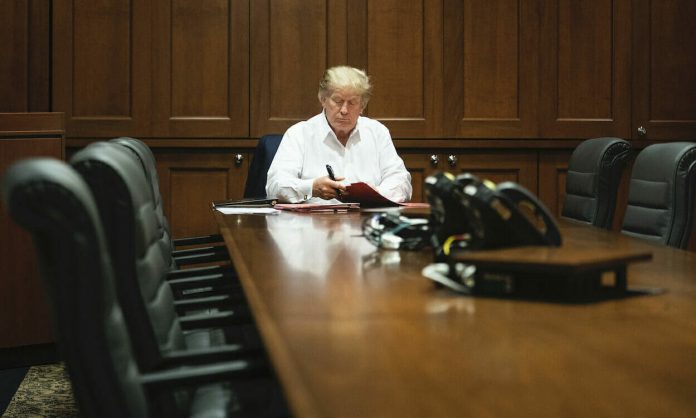
A go-to strategy among cyberattackers is developing phishing lures based on timely news events. Sure enough, threat researchers have spotted a moderate-volume malware campaign that’s been trying to trick users into downloading weaponized documents by promising the inside scoop on President Donald Trump’s coronavirus diagnosis.
Businesses should remind their employees to resist interacting with emails sent from unknown sources, especially when their subject lines and content promise inside information on current events. But the temptation is sometimes too much for users to resist.
“Everything we know and what we don’t about president’s COVID condition,” said one sample email from the campaign, which was reported by Proofpoint this week, which then provided a password to access the “coded” data.
Sherrod DeGrippo, senior director of threat research and detection at Proofpoint, told SC Media that the company over the past several months has seen an influx of phishing communications promising secret information about the virus.
“It’s a really good lure when you think about it,” DeGrippo said. “There’s this angle of conspiracy and ‘the government is hiding things from you’ that causes people to click a lot of times.” This scam heightens this strategy further by involving the U.S. president.
Often with COVID-19, malicious actors attempt to leverage the psychology of fear to induce potential victims into clicking on emails. But in this case, the adversaries appear to be preying on another common human condition – curiosity.
Social engineering always has some emotional hook,” said DeGrippo. In this case, she said, the hook is: “We’re letting you in on something.”
DeGrippo said that in addition to keeping employees aware of these kind of scams, organizations should be investing in technical controls to stop these emails before they reach in-boxes in the first place.
The phishing campaign was comprised of about 5,000 communications that were distributed among roughly 1,000 organizations spread among 72 different verticals, primarily based in the U.S. and Canada. All of the links within the emails led to Google Docs landing pages, where potential victims were instructed to download an Excel file containing malicious macros. Enabling those macros would result in the downloading of Bazaloader.
“Bazaloader is a pretty classic modular downloader, which means that once it is installed on the machine the threat actor can send multiple later payloads,” DeGrippo explained. The malware is also linked to the actors behind the TrickBot banking trojan.
The combined use of the Excel document, macros and password actually helps sell the idea that the document might actually contain some juicy, secretive information, DeGrippo noted. Recipients think, “‘I have to put in a password, I have to enable this content.’ It all kind of flows together with this idea of, ‘Oh, this is secure information,’ when in fact it’s malicious content.”
Using Google Docs also helps the malicious actors because they can abuse the online service’s analytics to see victim engagement metrics, and then make tweaks to the campaign to make it more effective.
The adversaries have used roughly 30 different subject lines in their campaign. Examples include: “Recent material pertaining to the president’s illness,” “Newest information about the president’s condition,” and “Newest info pertaining to President’s illness.” The use of multiple subject lines helps the attackers evade attempts to block the emails, but also allows the adversaries to see which lure is the most effective and perhaps use that one more frequently in the next wave of communications, DeGrippo said.
If opened, the Excel spreadsheet is actually entirely empty, even after the macros are enabled. It contains no actual insider information on Trump’s illness – not even fake content.
DeGrippo said she expects “we’ll see more and more” of these types of campaigns in the days leading up to the presidential election.