Researchers have provided a case study on Nefilim, a ransomware operator that uses “double-extortion” tactics to ensure payment from victim organizations.
Ransomware is a form of malware that is created to encrypt compromised systems. Once it lands on a vulnerable machine — whether through a phishing message, software vulnerability, stolen access credentials, or other means — files and drives will be encrypted and can only be recovered with a decryption key.
The decryption key is the carrot dangled in front of victims, who are usually promised a key and the means to restore their systems in return for payment. When it comes to enterprise players, ransom demands can reach millions of dollars — and there is never a guarantee a key will be issued or will be technically suitable for restoration efforts.
The phrase “ransomware” has become a familiar one to the general public as week-on-week we hear of more cases.
In recent months, Colonial Pipeline suffered a ransomware outbreak that ended up causing fuel shortages across parts of the United States, and following an infection at Ireland’s national health service, the HSE is still experiencing “significant” disruption.
What makes ransomware different is the possibility of “double-extortion,” a relatively new tactic designed to ramp up the pressure on victims to pay up. During a cyberattack, ransomware operators including Maze, Nefilim, REvil, and Clops will steal confidential data and threaten to release or sell this information on a leak website.
On Tuesday, Trend Micro published a case study examining Nefilim, a ransomware group the researchers believe is, or was, associated with Nemty originally as a ransomware-as-a-service (RaaS) outfit.
Nemty appeared on the scene in 2019, but together with Sentinel Labs, Trend Micro says that Nefilim originated in March 2020.
Both actors, tracked by the firm as “Water Roc,” offered RaaS subscription services based on a 70/30 split, with margins reduced to 90/10 when high-profile victims were snagged by affiliates.
Trend Micro says that Nefilim often focuses on exposed Remote Desktop Services (RDP) services and public proof-of-concept (PoC) exploit code for vulnerabilities. These include CVE-2019-19781 and CVE-2019-11634, both of which are known bugs in Citrix gateway devices that received patches in 2020.
However, when unpatched services are found, exploit code is launched and initial access is obtained. Nefilim begins by downloading a Cobalt Strike beacon, Process Hacker — used to terminate endpoint security agents — the Mimikatz credentials dumper, and additional tools.
In one case documented by the team, Nefilim was also able to take advantage of CVE-2017-0213, an old vulnerability in Windows Component Object Model (COM) software. While a patch was issued back in 2017, the bug was still present and allowed the group to escalate their privileges to administrator levels.
The ransomware operators may also leverage stolen or easily-forced credentials to access corporate networks and for lateral movement.
MEGAsync may be used to exfiltrate data during attacks. Nefilim ransomware will then be deployed and will begin encrypting content. Extensions vary, but the group has been linked to the extensions .Nephilim, Merin, and .Off-White.
A random AES key for each file queued for encryption is generated. The malware will then decrypt a ransom note using a fixed RC4 key which provides email addresses for victims to contact them concerning payment.
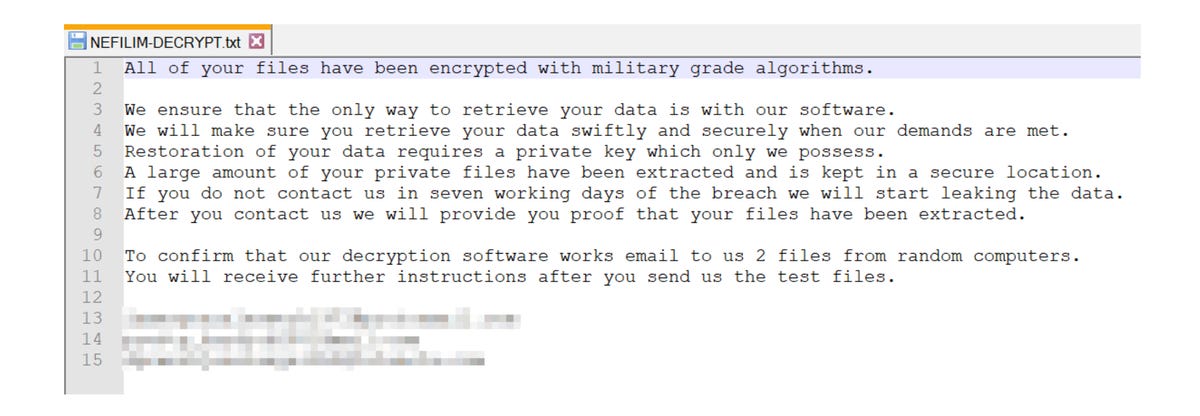
“To enable file decryption in case the victim pays the ransom amount, the malware encrypts the generated AES key with a fixed RSA public key and appends it to the encrypted file,” the researchers say. “To date, only the attackers can decrypt this scheme as they alone own the paired private RSA key.”
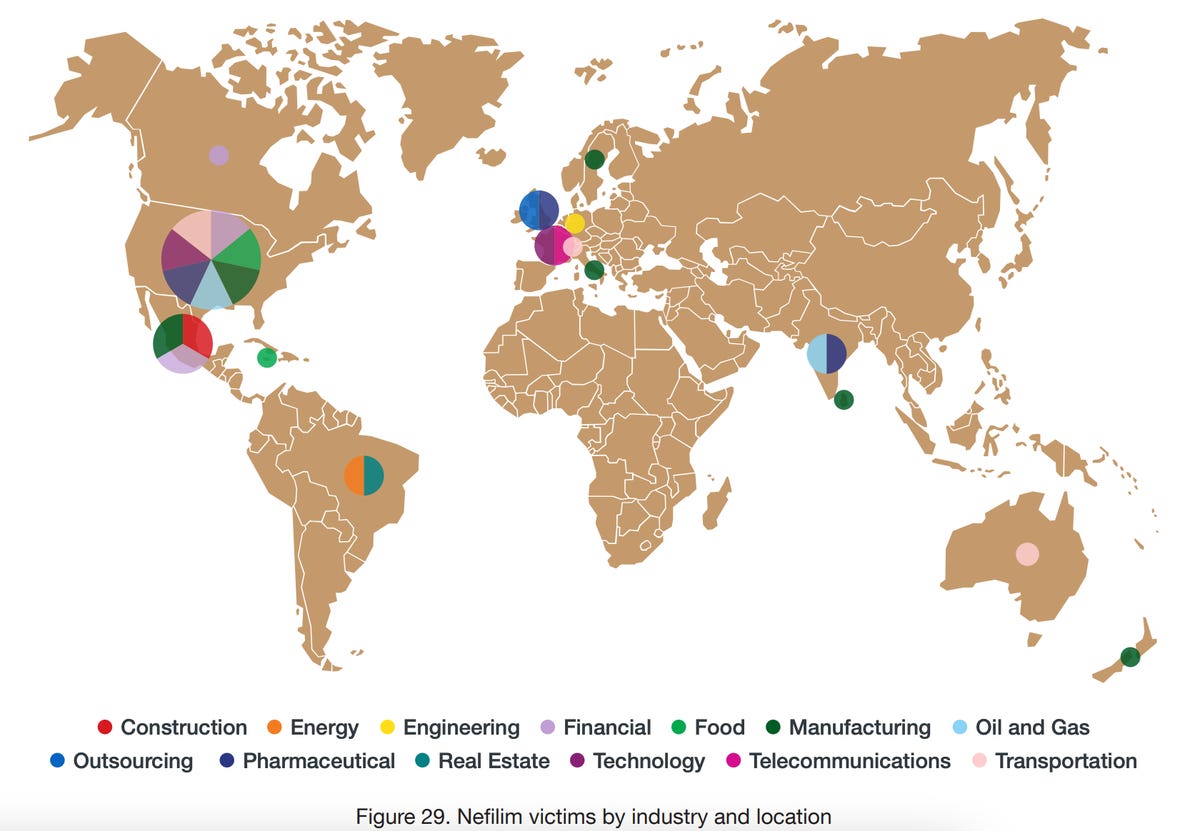
When it comes to victims, Nefilim has been connected most often with attacks against organizations generating an annual revenue of $1 billion or more; however, the malware operators have also struck smaller companies in the past.
The majority of victims are in the US, followed by Europe, Asia, and Oceania.
“Modern attackers have moved on from widespread mass-mailed indiscriminate ransomware to a new model that is much more dangerous,” Trend Micro says. “Today, corporations are subject to these new APT-level ransomware attacks. In fact, they can be worse than APTs because ransomware often ends up destroying data, whereas information-stealing APTs are almost never destructive. There is a more pressing need to defend organizations against ransomware attacks, and now, the stakes are much higher.”
Previous and related coverage
Have a tip? Get in touch securely via WhatsApp | Signal at +447713 025 499, or over at Keybase: charlie0











