Researchers say a platform used to connect artists and potential buyers leaked the personally identifiable information (PII) of users.
On Friday, the WizCase team, led by Ata Hakçıl, said that misconfigurations in an Amazon S3 bucket belonging to Artwork Archive exposed over 200 000 files.
Based in Denver, Colorado, Artwork Archive is marketed as a platform to “give artists, collectors, and organizations a better way to manage their art.” Software solutions are offered on a subscription basis to manage both the purchase and sale of artwork.
The security researchers discovered the bucket, which did not require any authentication to access, on May 23.
In total, 421GB of data was exposed. Dating back to August 2015, the records related to over 7000 artists, collectors, and galleries, and “potentially their customers, too,” according to WizCase. Data available to view included full names, physical addresses, and email addresses.
Purchase details, too, were exposed. WizCase found approximately 9000 invoices, as shown below, including the price of artwork and sales agreements, alongside revenue reports.
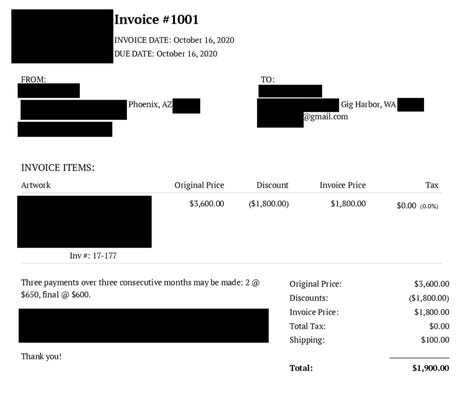
WizCase
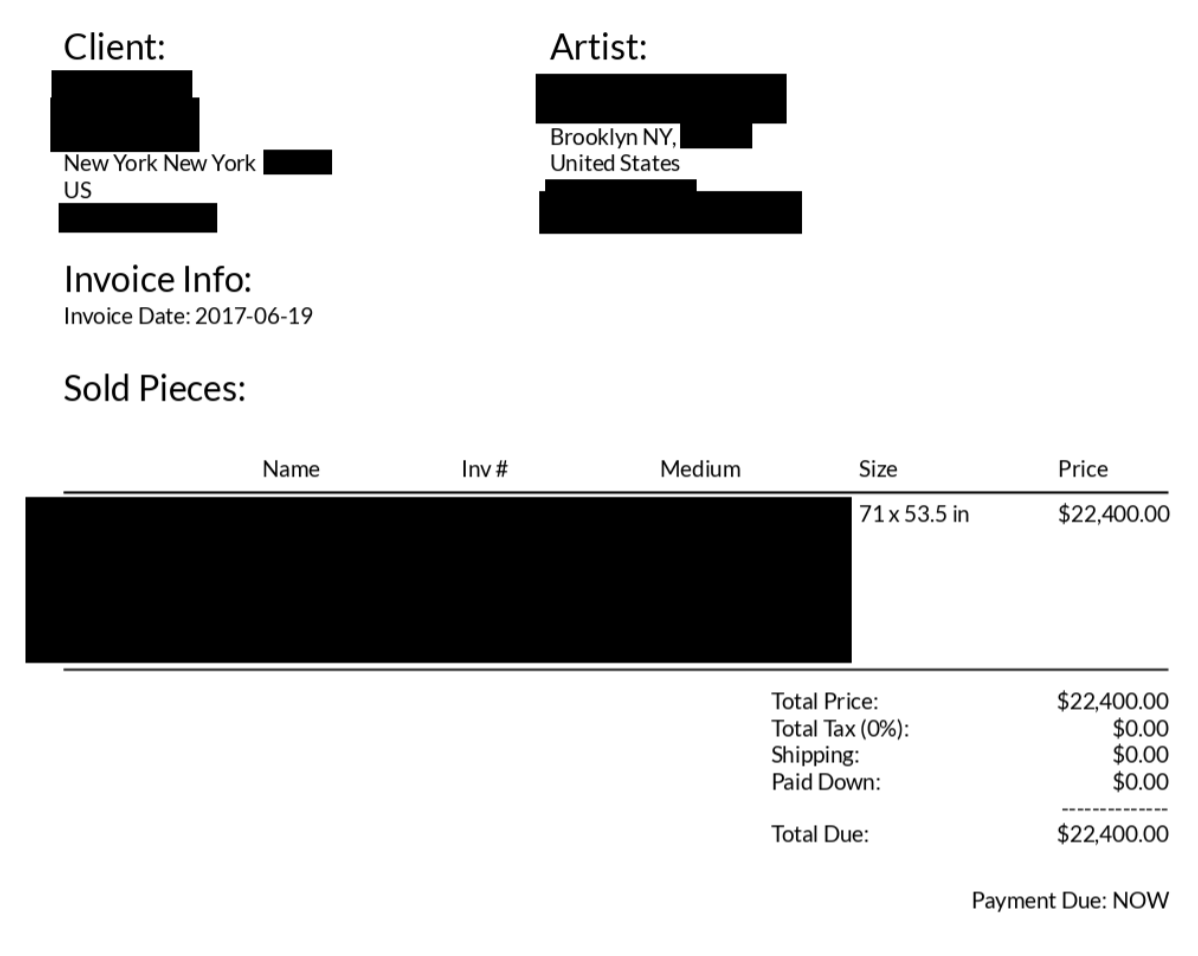
WizCase
In addition, “exported contacts” were stored in the bucket, containing full names, phone numbers, email addresses, city and country, and company affiliations of individuals.
“These were usually contacts an artist added to Artwork Archive via their contact management feature and included art institutions, individual artists, art collectors, friends, and family,” the researchers say.
Finally, WizCase discovered inventory reports which listed artwork owned by “specific artists, buyers, and galleries.”
Artwork Archive was made aware of the security issue on May 23 and secured the storage system three days later, on May 26.
ZDNet has reached out to Artwork Archive, and we will update when we hear back.
Previous and related coverage
Have a tip? Get in touch securely via WhatsApp | Signal at +447713 025 499, or over at Keybase: charlie0










