Malware delivered over the cloud increased by 68% in Q2, according to data from cybersecurity firm Netskope.
The company released the fifth edition of its Cloud and Threat Report that covers the cloud data risks, threats and trends they see throughout the quarter.
The report noted that cloud storage apps account for more than 66% of cloud malware delivery.
“In Q2 2021, 43% of all malware downloads were malicious Office docs, compared to just 20% at the beginning of 2020. This increase comes even after the Emotet takedown, indicating that other groups observed the success of the Emotet crew and have adopted similar techniques,” the report said.
“Collaboration apps and development tools account for the next largest percentage, as attackers abuse popular chat apps and code repositories to deliver malware. In total, Netskope detected and blocked malware downloads originating from 290 distinct cloud apps in the first half of 2021.”
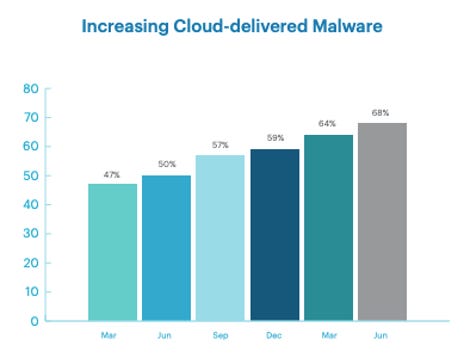
Netskope
The researchers behind the report explained that cybercriminals deliver malware through cloud apps “to bypass blocklists and take advantage of any app-specific allow lists.” Cloud service providers generally remove most malware immediately, but some attackers have found ways to do significant damage in the short time they spend undetected in a system.
According to the company’s researchers, about 35% of all workloads are also exposed to the public internet within AWS, Azure, and GCP, with public IP addresses that are reachable from anywhere on the internet.
RDP servers — which they say have become “a popular infiltration vector for attackers” — were exposed in 8.3% of workloads. The average company with anywhere between 500 and 2000 employees now deploys 805 distinct apps and cloud services, with 97% of those being “unmanaged and often freely adopted by business units and users.”
The rapid adoption of enterprise cloud apps has continued into 2021, with data showing adoption is up 22% for the first half of the year. But, the report notes that “97% of cloud apps used in the enterprise are shadowing IT, unmanaged and often freely adopted by business units and users.”
There are also issues raised in the report about employee habits, both at the workplace and at home. The report raises concerns about the nearly universal trend of employees authorizing at least one third-party app in Google Workspace.
Netskope’s report says employees leaving an organization upload three times more data to their personal apps in the final 30 days of employment.
The uploads are leaving company data exposed because much of it is uploaded to personal Google Drive and Microsoft OneDrive, which are popular targets for cyberattackers. According to Netskope’s findings, 15% “either upload files that were copied directly from managed app instances or that violate a corporate data policy.”
The researchers also add that remote work is still in full swing as of the end of June 2021, with 70% of users surveyed still working remotely.
“At the beginning of the pandemic, when users began working from home, we saw a spike in users visiting risky websites, including adult content, file sharing, and piracy websites,” the report added.
“Over time, this risky web surfing subsided as users presumably became more accustomed to working from home, and IT teams were able to coach users on acceptable use policies.”
The report touts the decline in risky browsing but also highlights the “growing danger of malicious Office documents” and cloud configurations as particularly thorny problems.
Joseph Carson, chief security scientist and advisory CISO at ThycoticCentrify, said the change to a hybrid work environment last year meant that cybersecurity needed to evolve from being perimeter and network-based to one that is focused on cloud, identity and privileged access management.
“Organizations must continue to adapt and prioritize managing and securing access to the business applications and data, such as that similar to the BYOD types of devices, and that means further segregation networks for untrusted devices but secured with strong privileged access security controls to enable productivity and access,” Carson said.











