HP released its latest Wolf Security Threat Insights Report, finding evidence that cybercriminals are moving even faster in taking advantage of zero-day vulnerabilities and exploiting specific problems like CVE-2021-40444 — the remote code execution vulnerability targeting the MSHTML browser engine through Microsoft Office documents.
The HP Wolf Security threat research team first discovered cyberattackers exploiting CVE-2021-40444 on September 8, one week before Microsoft issued a patch. By September 10, attackers had already created scripts designed to automate the creation of this exploit and shared it on GitHub.
The devastating attack gives cybercriminals a startlingly easy entry point into systems, deploying malware through an Office document that only needs to be previewed to be initiated.
HP researchers compile the report by analyzing the millions of endpoints running HP Wolf Security. In the latest report, the researchers found that 12% of email malware isolated had bypassed at least one gateway scanner and 89% of malware detected was delivered via email, while web downloads were responsible for 11%.
The most common attachments used to deliver malware were archive files, which HP Wolf researchers said increased in ubiquity from 17.26% last quarter to 38% this quarter.
Word documents are also used in 23% of instances while spreadsheets (17%), and executable files (16%) rounded out the list.
The report found that the top five most common phishing lures all used business lingo to lure victims in. Words like “order”, “payment”, “new”, “quotation” and “request” were used prolifically in attacks. The report found 12% of malware captured was previously unknown.
Alex Holland, the senior malware analyst with the HP Wolf Security threat research team, said the average time for a business to apply, test and fully deploy patches with the proper checks is 97 days, giving cybercriminals an opportunity to exploit this ‘window of vulnerability’.
“While only highly capable hackers could exploit this vulnerability at first, automated scripts have lowered the bar for entry, making this type of attack accessible to less knowledgeable and resourced threat actors. This increases the risk to businesses substantially, as zero-day exploits are commoditized and made available to the mass market in venues like underground forums,” Holland said.
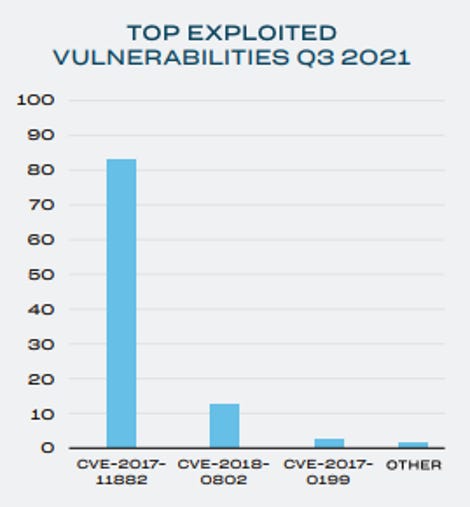
“Such novel exploits tend to be effective at evading detection tools because signatures may be imperfect and become obsolete quickly as the understanding of the scope of an exploit changes. We expect threat actors to adopt CVE-2021-40444 as part of their arsenals, and potentially even replace common exploits used to gain initial access to systems today, such as those exploiting Equation Editor.”
HP
Holland added that his team is seeing major platforms like OneDrive allowing hackers to conduct ‘flash in the pan’ attacks. While malware hosted on such platforms are generally taken down quickly, this does not deter attackers because they can often achieve their objective of delivering malware in the few hours the links are live, Holland explained.
“Some threat actors are changing the script or file type they are using every few months. Malicious JavaScript and HTA files are nothing new, but they are still landing in employee inboxes, putting the enterprise at risk. One campaign deployed Vengeance Justice Worm, which can spread to other systems and USB drives,” Holland said.
The HP Wolf team also found cybercriminals exploiting Cloud and web providers to host malware as well as multiple malware families being hosted on Discord and other gaming social media platforms.
The report outlines how new Javascript malware has been able to slip past detection tools via malicious email attachments.
One campaign uncovered by the HP Wolf Security threat research team found cybercriminals pretending to be part of the Ugandan National Social Security fund and using a spoofed web address similar to an official domain name to lure targets to a site that downloads a malicious Word document.
According to the report, Trickbot Trojans are also being delivered through HTA files now, which initiate the malware once the file is opened.
Ian Pratt, global head of security for personal systems at HP said relying on detection alone will no longer be sufficient because the threat landscape is too dynamic and attackers are increasingly adept at evading detection
“Organizations must take a layered approach to endpoint security, following zero trust principles to contain and isolate the most common attack vectors like email, browsers, and downloads,” Pratt said.
“This will eliminate the attack surface for whole classes of threats while giving organizations the breathing room needed to coordinate patch cycles securely without disrupting services.”













