Vidar malware has been detected in a new phishing campaign that abuses Microsoft HTML help files.
On Thursday, Trustwave cybersecurity researcher Diana Lopera said the spyware is being concealed in Microsoft Compiled HTML Help (CHM) files to avoid detection in email spam campaigns.
Vidar is Windows spyware and an information stealer available for purchase by cybercriminals. Vidar can harvest OS & user data, online service and cryptocurrency account credentials, and credit card information.
While often deployed through spam and phishing campaigns, researchers have also spotted the C++ malware being distributed through the pay-per-install PrivateLoader dropper, and the Fallout exploit kit.
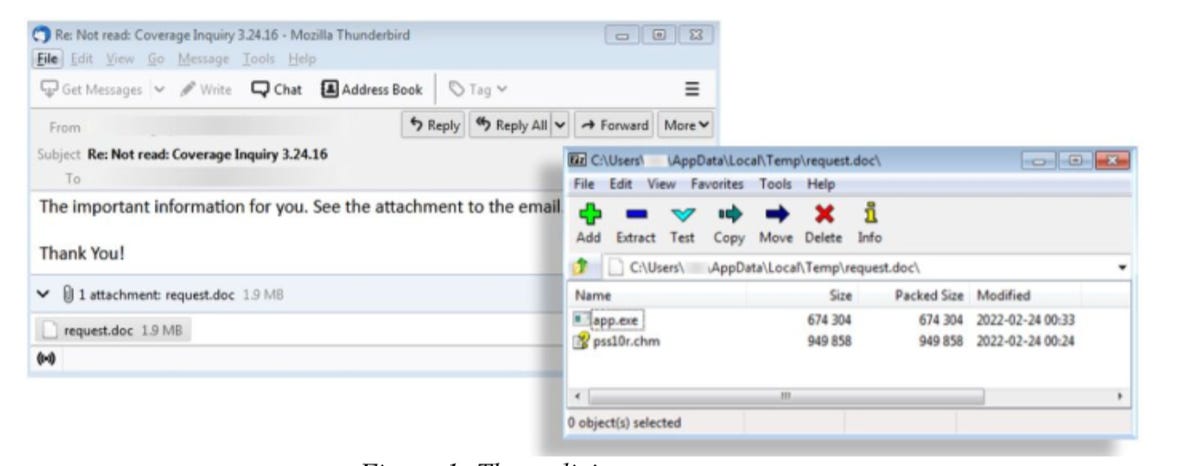
According to Trustwave, the email campaign distributing Vidar is far from sophisticated. The email contains a generic subject line and an attachment, “request.doc,” which is actually a .iso disk image.
Trustwave
The .iso contains two files: a Microsoft Compiled HTML Help (CHM) file (pss10r.chm) and an executable (app.exe).
The CHM format is a Microsoft online extension file for accessing documentation and help files, and the compressed HTML format may hold text, images, tables, and links — when used legitimately.
However, when attackers exploit CHM, they can use the format to force Microsoft Help Viewer (hh.exe) to load CHM objects.
When a malicious CHM file is unpacked, a JavaScript snippet will silently run app.exe, and while both files have to be in the same directory, this can trigger the execution of the Vidar payload.
The Vidar samples obtained by the team connect to their command-and-control (C2) server via Mastodon, a multi-platform open source social networking system. Specific profiles are searched, and C2 addresses are grabbed from user profile bio sections.
This allows the malware to set up its configuration and get to work harvesting user data. In addition, Vidar was observed downloading and executing further malware payloads.
See also
Have a tip? Get in touch securely via WhatsApp | Signal at +447713 025 499, or over at Keybase: charlie0












