Google Uncovers APT41’s Use of Open Source GC2 Tool to Target Media and Job...
By:
Apr 17, 2023Ravie LakshmananCyber Threat / Cloud Security
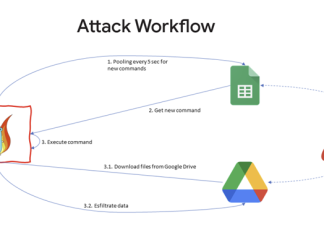
A Chinese nation-state group targeted an unnamed Taiwanese media organization to deliver an open source red teaming tool known as Google...
Safari Zero-Day Used in Malicious LinkedIn Campaign
Researchers shed light on how attackers exploited Apple web browser vulnerabilities to target government officials in Western Europe.
Threat actors used a Safari zero-day flaw to send malicious links...
Russian TrickBot Gang Hacker Extradited to U.S. Charged with Cybercrime
By: Ravie Lakshmanan
A Russian national, who was arrested in South Korea last month and extradited to the U.S. on October 20, appeared in a federal court in the state...
Twitter Denies Hacking Claims, Assures Leaked User Data Not from its System
By:
Jan 12, 2023Ravie LakshmananData Security / Privacy
Twitter on Wednesday said that its investigation found "no evidence" that users' data sold online was obtained by exploiting any security vulnerabilities...
Rising Demand for DDoS Protection Software Market By 2020-2028
By: The Hacker News
Distributed Denial of Service (DDoS) attack is a malicious form of attack that disrupts the regular network traffic by overwhelming the website with more traffic than...
New P2P Botnet Targeting IoT Devices
By: Ravie Lakshmanan
Cybersecurity researchers have taken the wraps off a new botnet hijacking Internet-connected smart devices in the wild to perform nefarious tasks, mostly DDoS attacks, and illicit cryptocurrency...
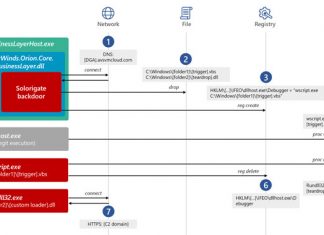
Here’s How SolarWinds Hackers Stayed Undetected for Long Enough
By: Ravie Lakshmanan
Microsoft on Wednesday shared more specifics about the tactics, techniques, and procedures (TTPs) adopted by the attackers behind the SolarWinds hack to stay under the radar and...
Telcom and BPO Companies Under Attack by SIM Swapping Hackers
By:
Dec 06, 2022Ravie LakshmananSIM Swapping / Network Intrusion
A persistent intrusion campaign has set its eyes on telecommunications and business process outsourcing (BPO) companies at lease since June 2022.
"The...
Two Eastern Europeans Sentenced for Providing Bulletproof Hosting to Cyber Criminals
By: Ravie Lakshmanan
Two Eastern European nationals have been sentenced in the U.S. for offering "bulletproof hosting" services to cybercriminals, who used the technical infrastructure to distribute malware and attack...
New York charity leaves sensitive patients’ data unsecured
We recently discovered an unsecured database that appears to belong to one of the largest charities in New York. The unsecured database contained more than 2,000 CSV and TXT...