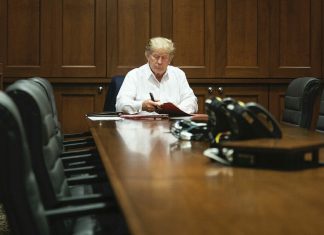
Phishing scam lures employees by teasing secrets of Trump COVID diagnosis
By:
Bradley Barth
A go-to strategy among cyberattackers is developing phishing lures based on timely news events. Sure...
LinkedIn Phishing Ramps Up With More-Targeted Attacks
Seeking to take advantage of out-of-work users, malware groups continue to use LinkedIn and business services to offer fictional jobs and deliver infections instead.Phishing attacks are targeting out-of-work users...
All You Need To Know About Form Based Phishing Attacks
Author: Kyle Fedorek
Phishing methods have witnessed an evolution in the current landscape, coercing users into offering credentials. Researchers have warned people to keep an eye out for form-based phishing...
JavaScript Obfuscation Moves to Phishing Emails
Attackers are hiding malicious payloads in phishing emails via a technique traditionally used to hide malicious code planted on websites.JavaScript, the ubiquitous scripting language used across Web applications worldwide,...
2020 was the year of phishing, with a jump of 510% in the first...
A new report shows a staggering 34.4% increase in phishing attacks in the last year.2020 was a bad year to be someone susceptible to phishing attacks, a massive collection...
Researchers Learn From Nation-State Attackers’ OpSec Mistakes
Security researchers discuss how a series of simple and consistent mistakes helped them learn more about ITG18, better known as Charming Kitten.When security intelligence teams talk about human error,...
LogoKit Group Aims for Simple Yet Effective Phishing
A phishing kit that uses embedded JavaScript targeted the users of more than 300 sites in the past week, aiming to grab credentials for SharePoint, Adobe Document Cloud, and...
Fraudsters Use HTML Legos to Evade Detection in Phishing Attack
Enterprise VulnerabilitiesFrom DHS/US-CERT's National Vulnerability Database
CVE-2021-29221PUBLISHED: 2021-04-09
A local privilege escalation vulnerability was discovered in Erlang/OTP prior to version 23.2.3. By adding files to an existing installation's directory, a local...
Intl. Law Enforcement Operation Takes Down DoubleVPN
The VPN service allegedly provided a means for cybercriminals to target their victims, Europol officials report.A coordinated international law enforcement operation has seized the Web domains and server infrastructure...