Image: Kashaf et al.
In 2016, Dyn, a provider of managed DNS servers, was the victim of a massive DDoS attack that crippled the company’s operations and took down domain-name-resolving operations for more than 175,000 websites.
While some sites managed to stay up by activating a redundancy and switching DNS resolving to secondary servers, many websites were not prepared and remained down for almost a day as Dyn dealt with the attack.
Also: Best web hosting services 2020: Wix, WordPress, and more
Four years later, a team of academics from Carnegie Mellon University have conducted a large-scale study of the top 100,000 websites on the internet to see how website operators reacted to this attack and how many are still operating with one single DNS provider and no other backup.
Their findings, published at the Internet Measurement Conference last month, show that, currently, in 2020, 89.2% of all websites use a third-party DNS provider rather than managing their own DNS server.
But even worse is the fact that 84.8% of all analyzed websites relied on one single DNS provider, without having a backup redundancy to which they could switch in case of a failure or attack.

Image: Kashaf et al.
The CMU team says the number of sites with a critical DNS dependency (no redundancy) has gone up by 4.7% since 2016, showing that the lessons site operators were supposed to learn following the Dyn DDoS attack lessons have been largely, and almost immediately, forgotten.
Researchers point out that while two websites (2%) in the Top 100 added backup DNS servers since 2016, smaller websites continued to use one single DNS service provider without a backup, and in most cases, many site operators chose to go with a known provider, contributing to a long-observed tendency of consolidation among internet service providers.
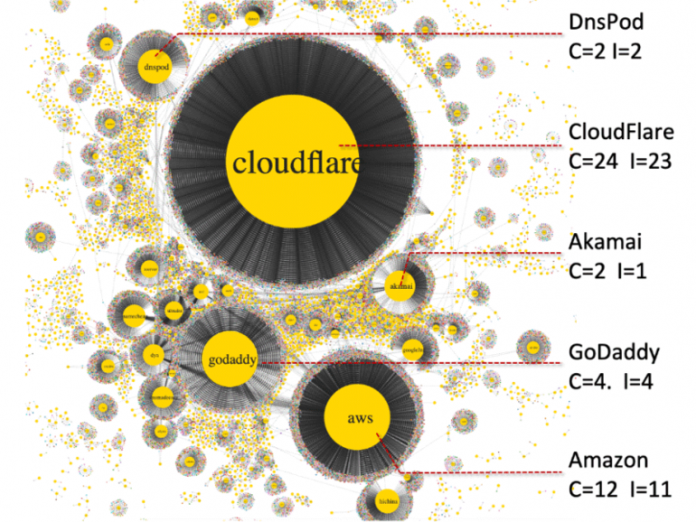
Currently, CMU researchers say that the Top-3 DNS providers —Cloudflare (24%), AWS (12%), and GoDaddy (4%)— are the single DNS providers of around 38% of the Top 100,000 sites in the Alexa ranking.
In addition, four DNS providers are the lone critical providers for more than half of the Alexa Top 100 website list.
Any intentional attack or accidental hardware or software failure at one of these three providers can bring down a large chunk of the internet with them, something that appears to happen once in a while [1, 2], still.
Furthermore, researchers point out that even if there are more than 10,000 DNS providers serving the Alexa Top 100k sites, most have indirect dependencies back to a handful of providers, such as Cloudflare, AWS, GoDaddy, Namecheap, Oracle (formerly Dyn), and others.
The researchers also not that of the website operators who chose to add a redundancy, most were customers of Dyn, NS1, UltraDNS, and DNSMadeEasy.
“This may be because these providers encourage the use of secondary DNS provider by giving specific guidelines to seamlessly incorporate a secondary DNS provider,” the research team noted.
“High redundancy for Dyn and NS1 customers could alsobe a result of large-scale attacks on Dyn and NS1.”
But the study took similar looks at the state third-party services and critical dependencies (no redundancies) for websites using CDNs (content delivery networks) and CAs (certificate authorities).
The results were similar to the team’s research on DNS, with many websites operating with either their CDN or CA OCSP stapling provider as a point of failure in their operations, without any backup redundancy.

Image: Kashaf et al.
Additional details about the team’s research are available in an academic paper titled “Analyzing Third Party Service Dependencies in Modern WebServices: Have We Learned from the Mirai-Dyn Incident?,” also available as a PDF document.
A video of the research team presenting its findings is available below.